blog
Reporting group membership for critical Active Directory groups
I work a lot with Active Directory-related tasks. One of the tasks is to know the group membership of critical Active Directory Groups such as Domain Admins, Enterprise Admins, Schema Admins, Event Log Readers, and a few others that are a bit less known. As I did it, I got bored of typing the group names repeatedly and decided that enough was enough and there must be an easier way for me to do that.
💡 Getting group membership from Critical AD Groups
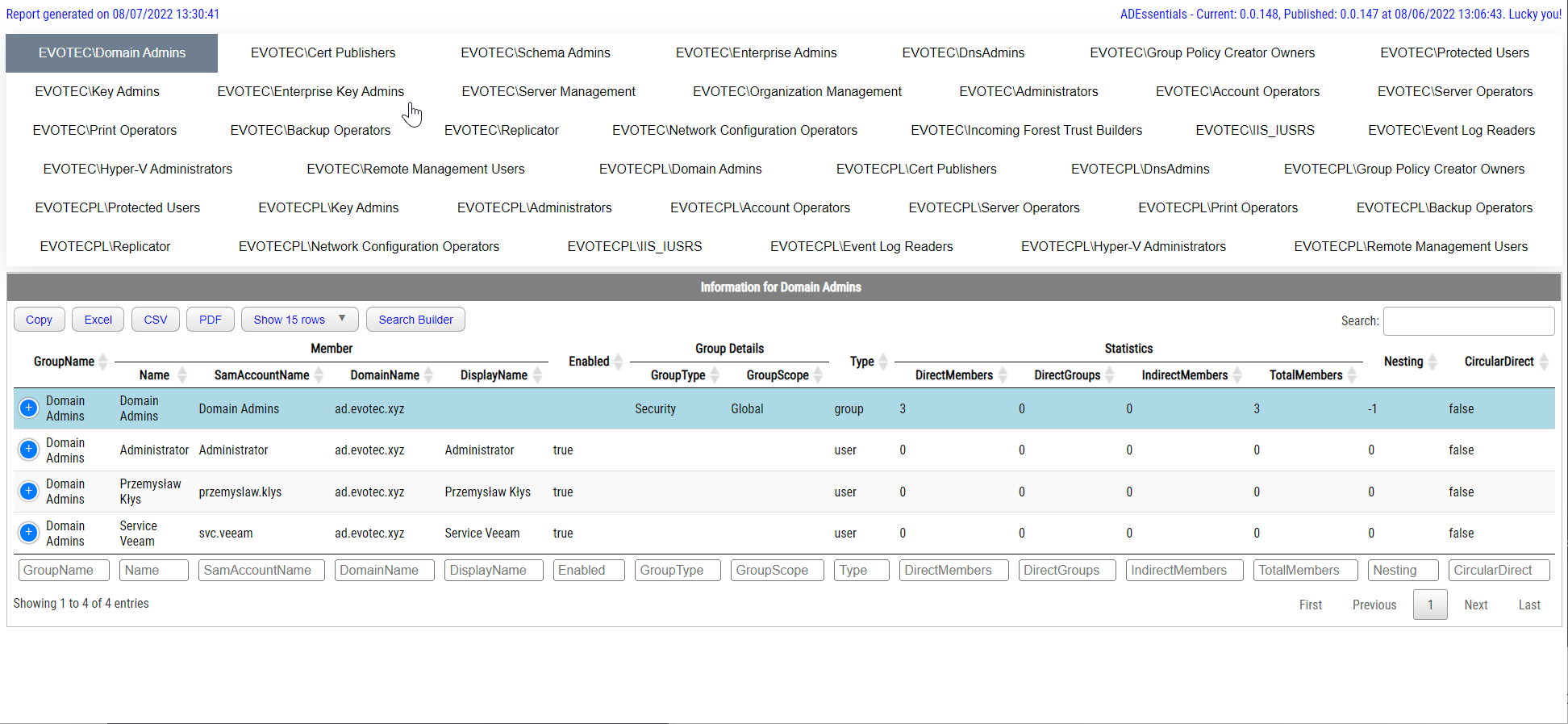
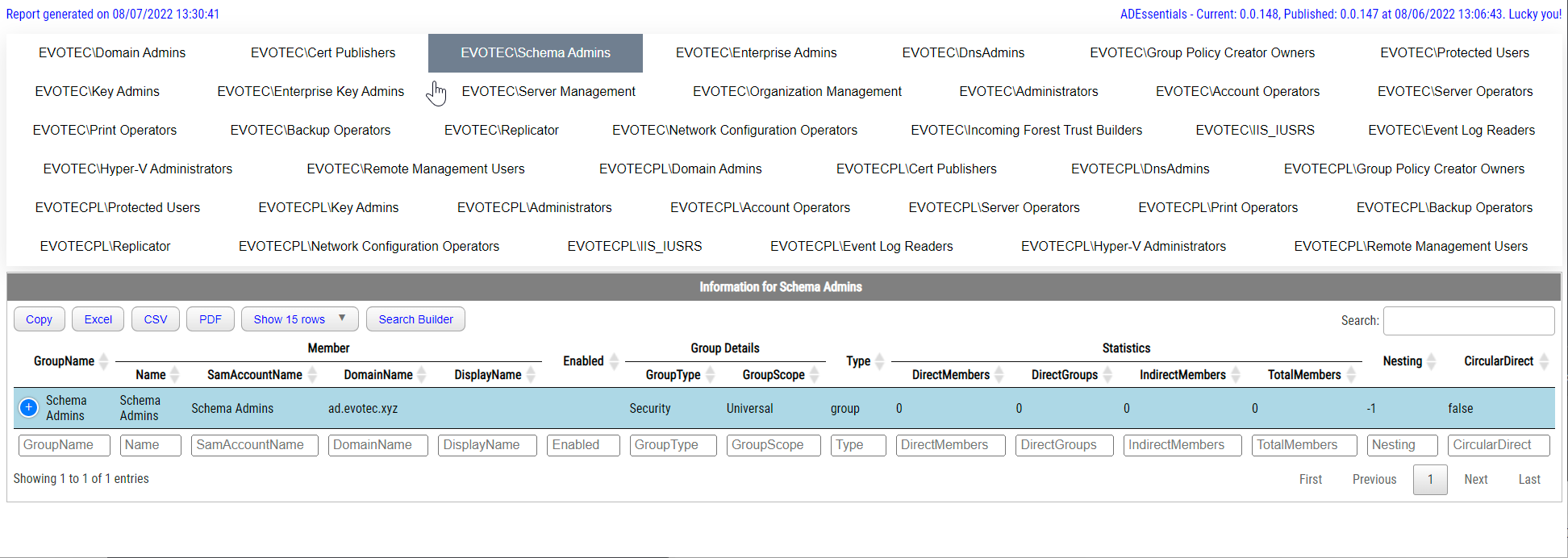
To do my automation, I've utilized functions shown in Visually display Active Directory nested Group Membership using PowerShell that is part of ADEssentials PowerShell Module. I've created a function called Show-WinADGroupCritical, which generates easy to use preview of all built-in critical groups in Active Directory.
Show-WinADGroupCritical -Verbose
It may take a while to generate, depending on how big your AD is and what sort of nightmare you hold in those groups.
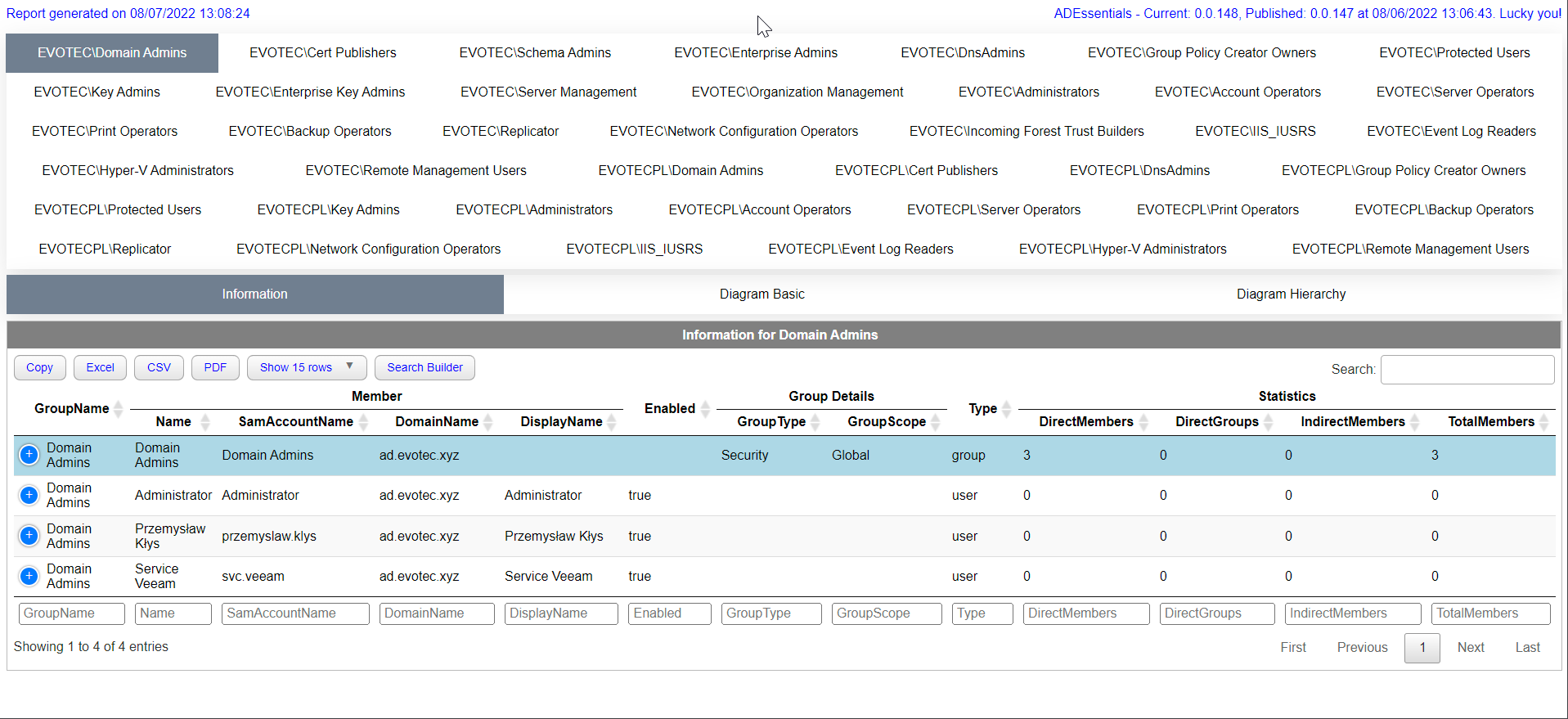

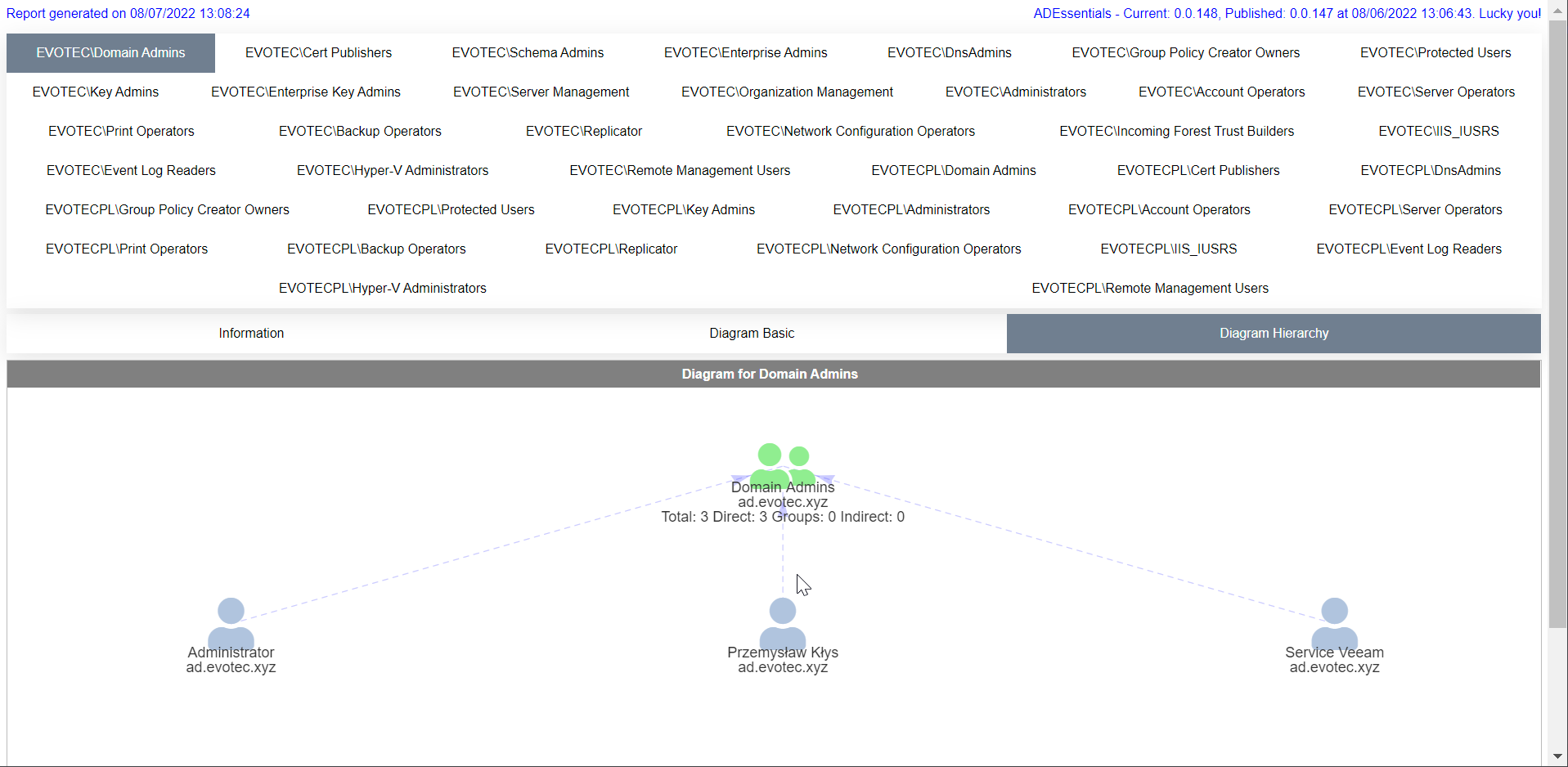
By default, the function auto-detects Active Directory Forest and scans all the domains and all the groups. Since those critical groups should be mostly empty, the default settings provided by the function should work just fine for everyone. Unfortunately, I often meet domains with not-so-clean states and recently had to add the SkipDiagram parameter, which allows me to skip generating diagrams if I meet a group with, say, 1500 nested groups. Unfortunately, with a large number of groups, the diagrams with that many groups become unreadable and challenging to load in HTML. So if you ever just want to find out nested group membership and all additional details without the need for diagrams or because the diagrams are slowing you down – you can use the SkipDiagram option just to get the meat you require.
Show-WinADGroupCritical -Verbose -FilePath $Env:UserProfile\Desktop\GroupReport.html -Online -SkipDiagram
I've used the Verbose parameter, which shows what is happening in the background, and FilePath to save the report into the specific path.
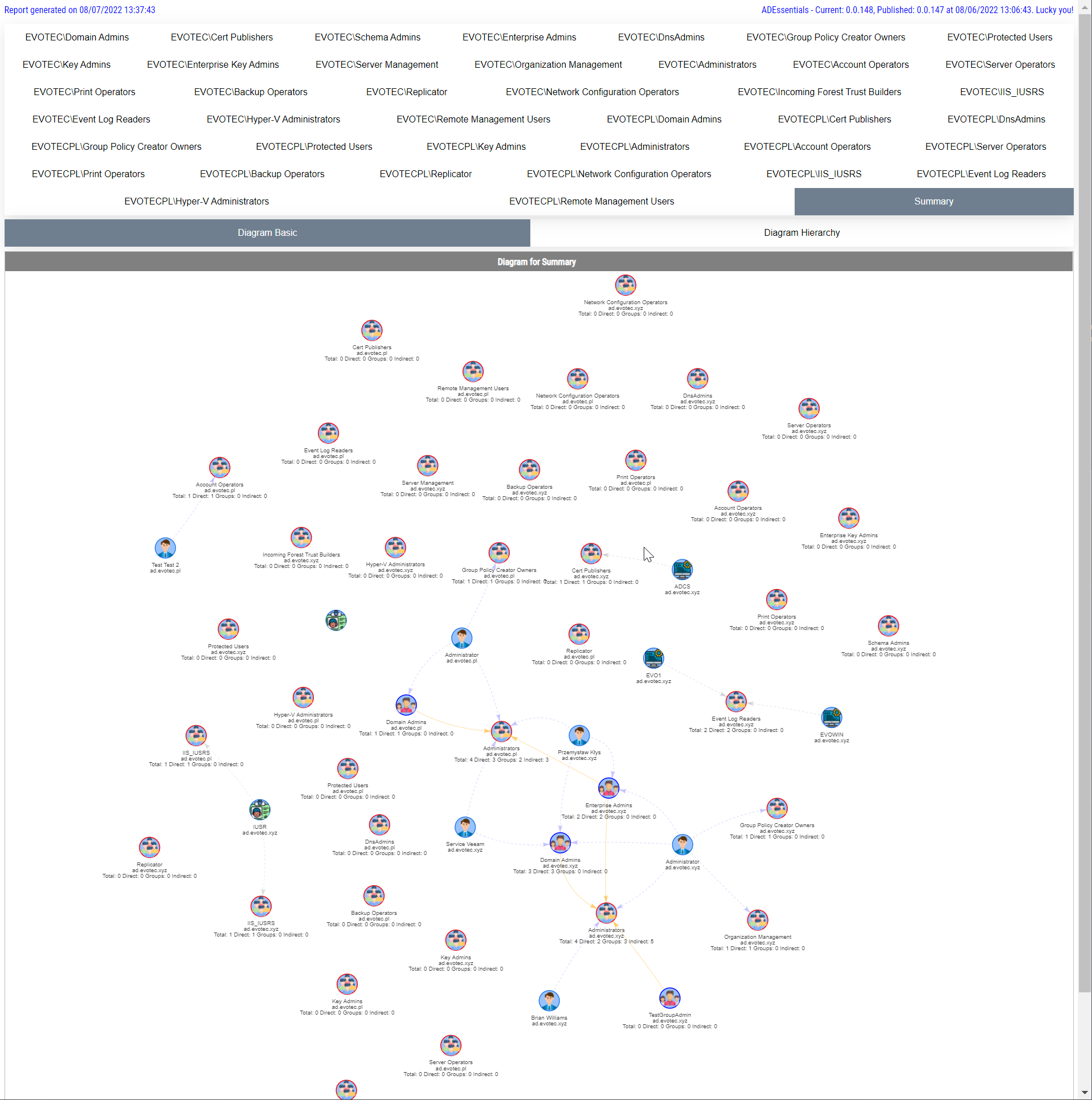
There's also a parameter called Summary, which bundles all groups into two diagrams and can show you the whole picture of all your critical groups and how they are connected (if at all).
Show-WinADGroupCritical -Verbose -FilePath $Env:UserProfile\Desktop\GroupReport.html -Online -Summary
Remember that you can also pick and choose groups you want to display from the defined critical groups. Just in case you're not interested in the full scope of your Forest.

Keep in mind that in the best-case scenario, those groups should be mostly empty with very few actual users in them, and primarily Administrative at that. If you have many users, nested groups, and service accounts, you may want to investigate why and if that's necessary.
💡 Available function options
get-help -Detailed Show-WinADGroupCritical
NAME
Show-WinADGroupCritical
SYNOPSIS
Command to gather nested group membership from default critical groups in the Active Directory.
SYNTAX
Show-WinADGroupCritical [[-GroupName] ] [[-FilePath] ] [[-HideAppliesTo] ] [-HideComputers]
[-HideUsers] [-HideOther] [-Online] [-HideHTML] [-DisableBuiltinConditions] [-AdditionalStatistics] [-SkipDiagram] [-Summary]
[]
DESCRIPTION
Command to gather nested group membership from default critical groups in the Active Directory.
This command will show data in table and diagrams in HTML format.
PARAMETERS
-GroupName
Group Name or Names to search for from provided list. If skipped all groups will be checked.
-FilePath
Path to HTML file where it's saved. If not given temporary path is used
-HideAppliesTo
Allows to define to which diagram HideComputers,HideUsers,HideOther applies to
-HideComputers []
Hide computers from diagrams - useful for performance reasons
-HideUsers []
Hide users from diagrams - useful for performance reasons
-HideOther []
Hide other objects from diagrams - useful for performance reasons
-Online []
Forces use of online CDN for JavaScript/CSS which makes the file smaller. Default - use offline.
-HideHTML []
Prevents HTML output from being displayed in browser after generation is done
-DisableBuiltinConditions []
Disables table coloring allowing user to define it's own conditions
-AdditionalStatistics []
Adds additional data to Self object. It includes count for NestingMax, NestingGroup, NestingGroupSecurity,
NestingGroupDistribution. It allows for easy filtering where we expect security groups only when there are nested
distribution groups.
-SkipDiagram []
Skips diagram generation and only displays table. Useful if the diagram can't handle amount of data or if the diagrams
are not nessecary.
-Summary []
Adds additional tab with all groups together on two diagrams
This cmdlet supports the common parameters: Verbose, Debug,
ErrorAction, ErrorVariable, WarningAction, WarningVariable,
OutBuffer, PipelineVariable, and OutVariable. For more information, see
about_CommonParameters (https:/go.microsoft.com/fwlink/?LinkID=113216).
💡 Installing ADEssentials
Those cmdlets are part of the ADEssentials module that I've been enhancing for some time now. All you need to do, to install it is:
Install-Module ADEssentials -Force -Verbose
Many commands in the ADEssentials module require RSAT (ActiveDirectory/GroupPolicy) to be present to work. Some cmdlets are ADSI based, so they don't need RSAT to work, but others from ADEssentials do.
When you install the module, it will also install PSWriteHTML and PSEventViewer. The first one is required for displaying output in HTML (tables/diagrams). The other one is a wrapper around Get-WinEvent and is used by some of the commands available within ADEssentials. Install-Module will do all that installation for you without doing anything except for the RSAT requirement, but if you're AD Admin, you should already have those up and ready to use. If you don't have admin rights on your workstation, it's still possible to use this module.
Install-Module ADEssentials -Scope CurrentUser
As those cmdlets described above are read-only, they don't require any rights in AD. I've been digesting my production environments using my standard ID. For sources, reporting issues, or feature requests, as always, visit GitHub. All my projects are hosted on it, and it's preferred method of providing support.