blog
Exchange 2013 powershell errors out, and Exchange 2013 ECP doesn’t work correctly
After Exchange 2013 system is updated or after reboot ECP / OWA and other IIS pages appear blank. Also Powershell is not able to open up, and event log is full of errors.
❗ Problem Description
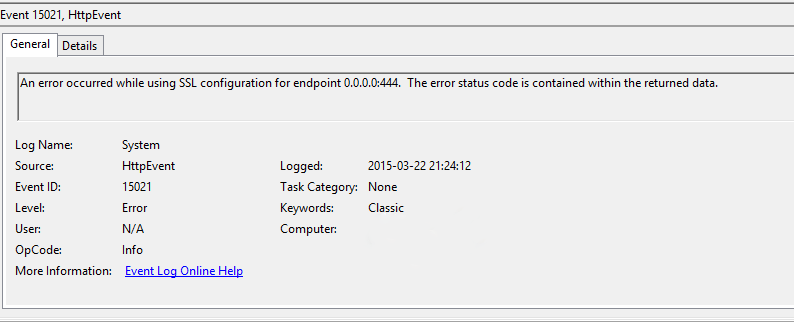
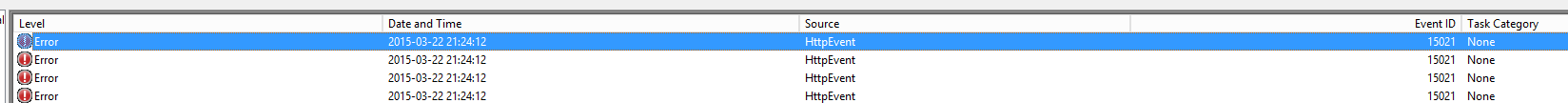
Exchange 2013 powershell errors out, and Exchange 2013 ECP doesn't work correctly (users get a login screen then a blank page). Moreover there is an EVENT being logged in Administrative Events (Event ID 15021, Source HttpEvent):
An error occurred while using SSL configuration for endpoint 0.0.0.0:444. The error status code is contained within the returned data.
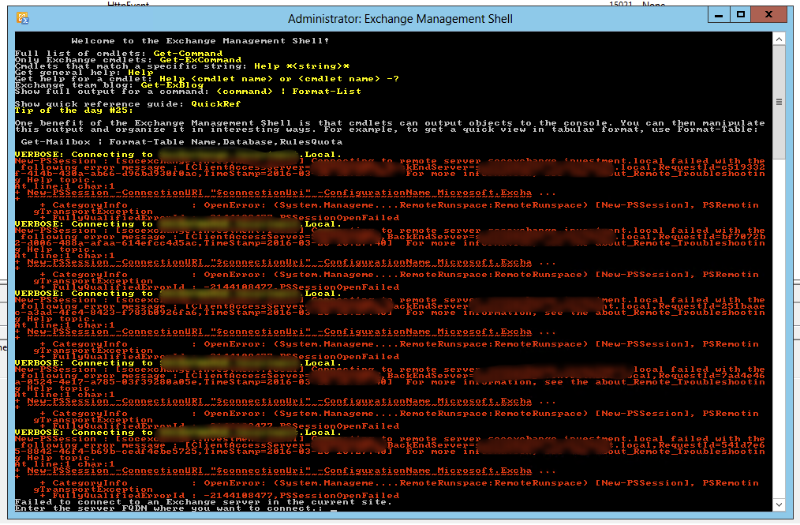
Error in PowerShell:
VERBOSE: Connecting to MAIL2. New-PSSession : [mail2] Connecting to remote server mail2 failed with the following error messa ge : [ClientAccessServer=MAIL2,BackEndServer=mail2,RequestId=fd9724cd-19fb-4842-b30d-c9c4b976119f,TimeStamp =2015-03-24 18:55:58] [FailureCategory=Cafe-SendFailure] For more information, see the about_Remote_Troubleshooting He lp topic. At line:1 char:1 + New-PSSession -ConnectionURI “$connectionUri” -ConfigurationName Microsoft CategoryInfo : OpenError: (System.Manageme….RemoteRunspace:RemoteRunspace) [New-PSSession], PSRemotin gTransportException + FullyQualifiedErrorId : -2144108477,PSSessionOpenFailed
Cause: This event is logged when an error occurred while using SSL configuration for socket address.The error status code is contained within the returned data.
🔑 Solution
Solution to solve it is to replace the certificate for 0.0.0.0:444 with the correct one. For some reason one of the certificates is being used instead of the one that is being served on standard https port.
- Click Start, point to All Programs, click Accessories, right-click Command Prompt, clickRun as administrator, and then click Continue.
- Type netsh http show sslcert, and then press ENTER to view the installed certificates.
- This will show the certs. Make a copy of the output to safe place.
- Under IP:port 127.0.0.1:443 note the certificate hash and application ID.
- Type netsh http delete sslcert ipport=0.0.0.0:444 (do this command even if the port doesn't exists on the list), and then press ENTER to delete the incorrectly installed certificate.
- netsh http add sslcert ipport=0.0.0.0:444 certhash= appid=” ”, and then press ENTER to reinstall the certificate.
- Reboot server
That's it. After rebooting certificate should be in it's place and content from Exchange being served correctly.