blog
Does GFI Mail Essentials 20.1 support full SPF specification
Sender Policy Framework (SPF) is a simple email-validation system designed to detect email spoofing by providing a mechanism to allow receiving mail exchangers to check that incoming mail from a domain comes from a host authorized by that domain's administrators. Even thou SPF does have a lot of it's own issues most large companies use it and it allows to filter out a lot of spam.
❗ Problem Description
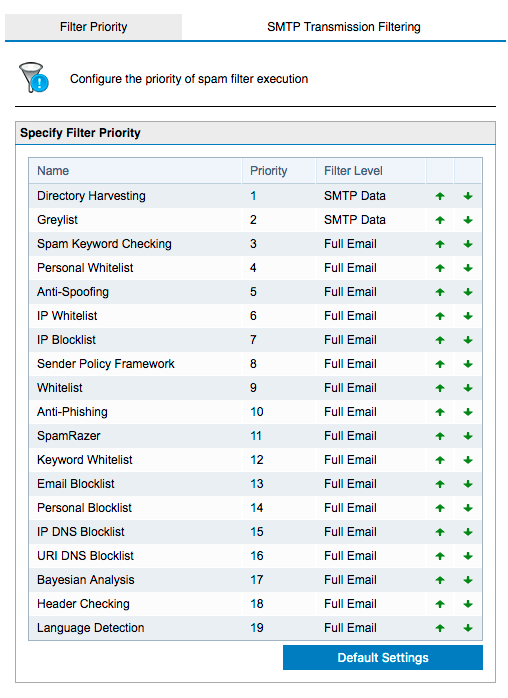
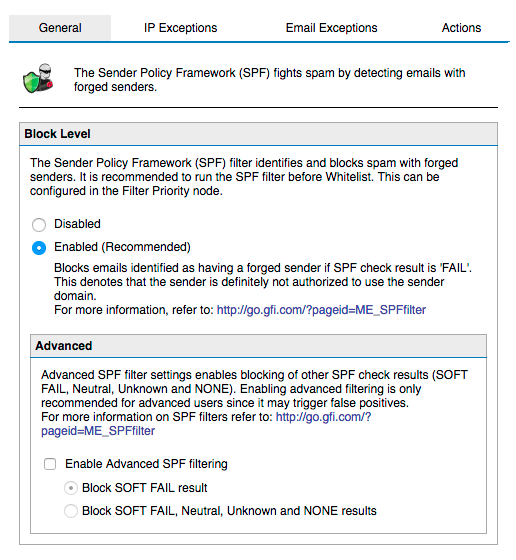
GFI Mail Essentials 20 does support SPF and it does so on two levels.
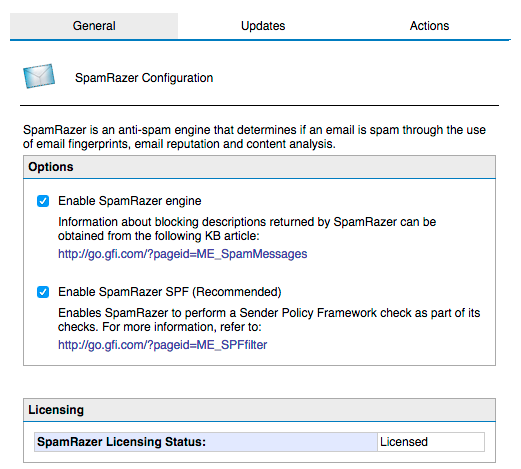
SpamRazer which is GFI very own special filter
Dedicated Sender Policy Framework
Imagine my surprise when I started seeing properly configured SPF for e-mails yet GFI reporting them as spam.
✅ Solution
After opening a case in GFI support system we were informed that:
GFI does support only basic SPF records
SpamRazer SPF filter does do some nested record lookups, but if it takes longer than a second to get a response, it will skip it
So if your customers use a bit more complicated SPF records you're gonna have lots of false positives. It includes even SPF for own gfi.com domain
“v=spf1 a:mailers.gfi.com a:oneconnectspf.gfi.com include:amazonses.com include:cleverbridge.com include:salesforce.com include:spf.protection.outlook.com”
“v=spf1 include:_spf-a.microsoft.com include:_spf-b.microsoft.com include:_spf-c.microsoft.com include:_spf-ssg-a.microsoft.com include:spf-a.hotmail.com ip4:147.243.128.24 ip4:147.243.128.26 ip4:147.243.1.153 ip4:147.243.1.47 ip4:147.243.1.48 -all”
“v=spf1 redirect=_spf.facebook.com”
“v=spf1 redirect=_spf.google.com”
“v=spf1 mx ptr:casses.aero ptr:s4a.aero include:_spf.google.com -all”
All those domains for gfi.com, microsoft.com, facebook.com or gmail.com most likely will fail GFI SPF testing… They even have have GFI voting system to support full RFC Specification for SPF. Don't hold your breath that it gets implemented anytime soon thou. So what to do until they add it properly?
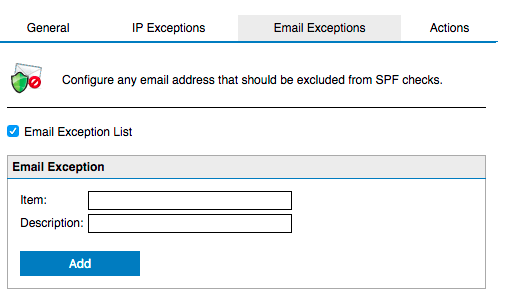
The only way to go for now is either disable it totally or add those domains to SPF Exception list (either by IP or e-mails – with wildcards being supported).
You should be aware that adding a domain to whitelist (whitelist ip, whitelist email or personal whitelist) will not skip SPF checking (unless SPF checking is below whitelist).