tags
laps
2 entries
Tags
Categories
2 entries
Backing up Bitlocker Keys and LAPS passwords from Active Directory
Back up BitLocker recovery keys and LAPS passwords from Active Directory so older restores and disaster recovery scenarios remain accessibl…
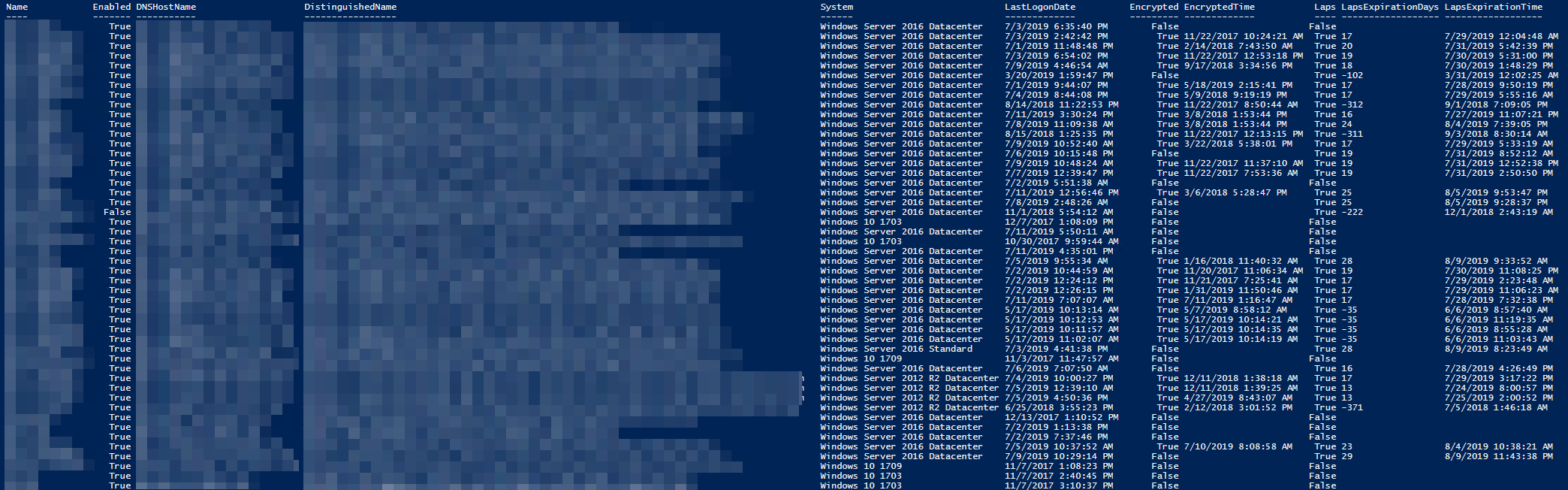
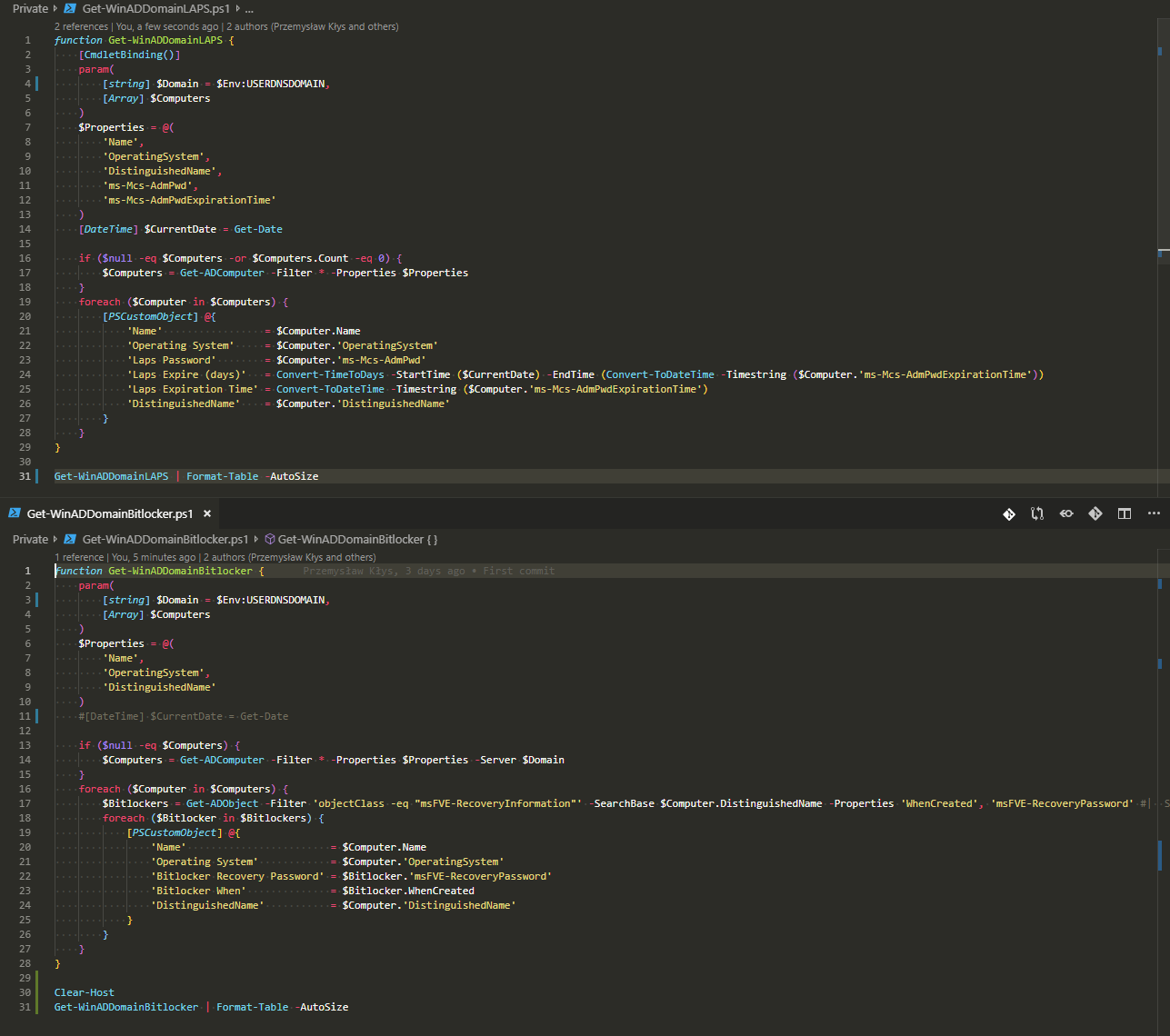
Getting Bitlocker and LAPS summary report with PowerShell
Having Bitlocker and LAPS in modern Active Directory is a must. But just because you enable GPO and have a process that should say Bitlocke…