categories
Active Directory
63 entries
20 entries

Accessing AzureVM with NLA and broken domain trust relationship
Regain access to Azure VMs after a broken domain trust by disabling NLA remotely and repairing the machine relationship with PowerShell.
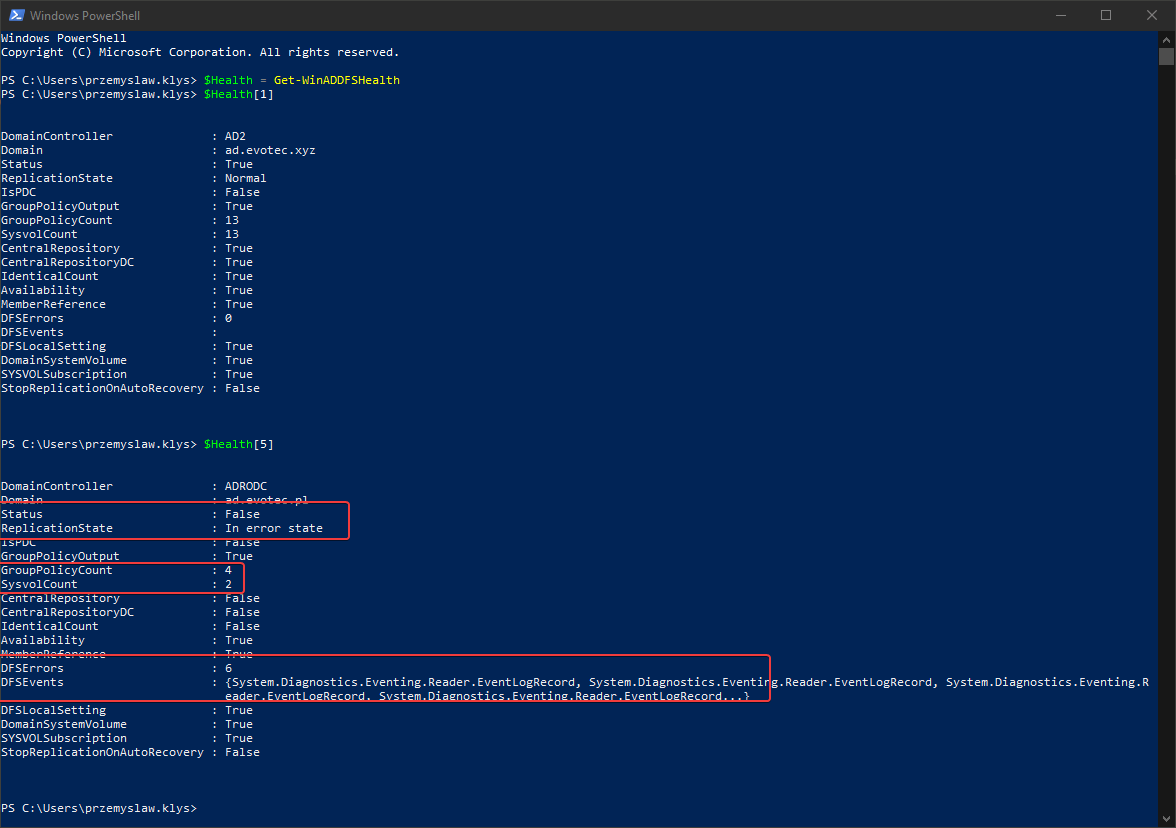
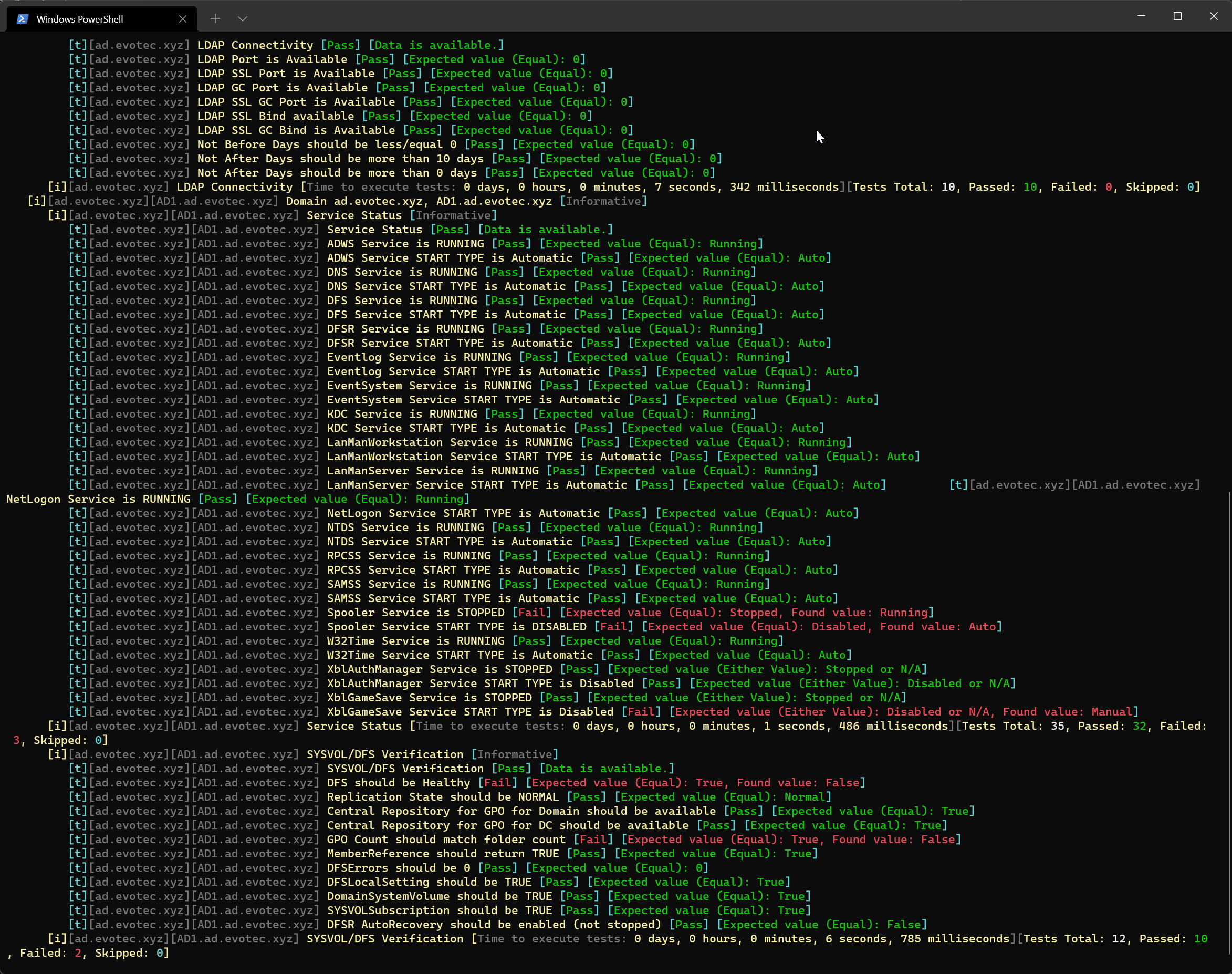
Active Directory DFS Health Check with PowerShell
One of the critical parts of Active Directory is DFS. It allows you to share same NETLOGON/SYSVOL folders across all Domain Controllers in…

Active Directory DHCP Report to HTML or EMAIL with zero HTML knowledge
I’m pretty addicted to reading blog posts. I saw this new blog post the other day, where the author created the DHCP HTML report, and he di…
Active Directory Domain Services could not replicate the directory partition – The replication operation encountered a database error
If you ever encounter an error while trying to create a new domain within a forest saying, “The replication operation encountered a databas…

Active Directory Health Check using Microsoft Entra Connect Health Service
Active Directory (AD) is crucial in managing identities and resources within an organization. Ensuring its health is pivotal for the seamle…

Active Directory Replication Summary to your Email or Microsoft Teams
Monitor Active Directory replication with Repadmin summaries delivered to email or Microsoft Teams so failures surface without manual check…
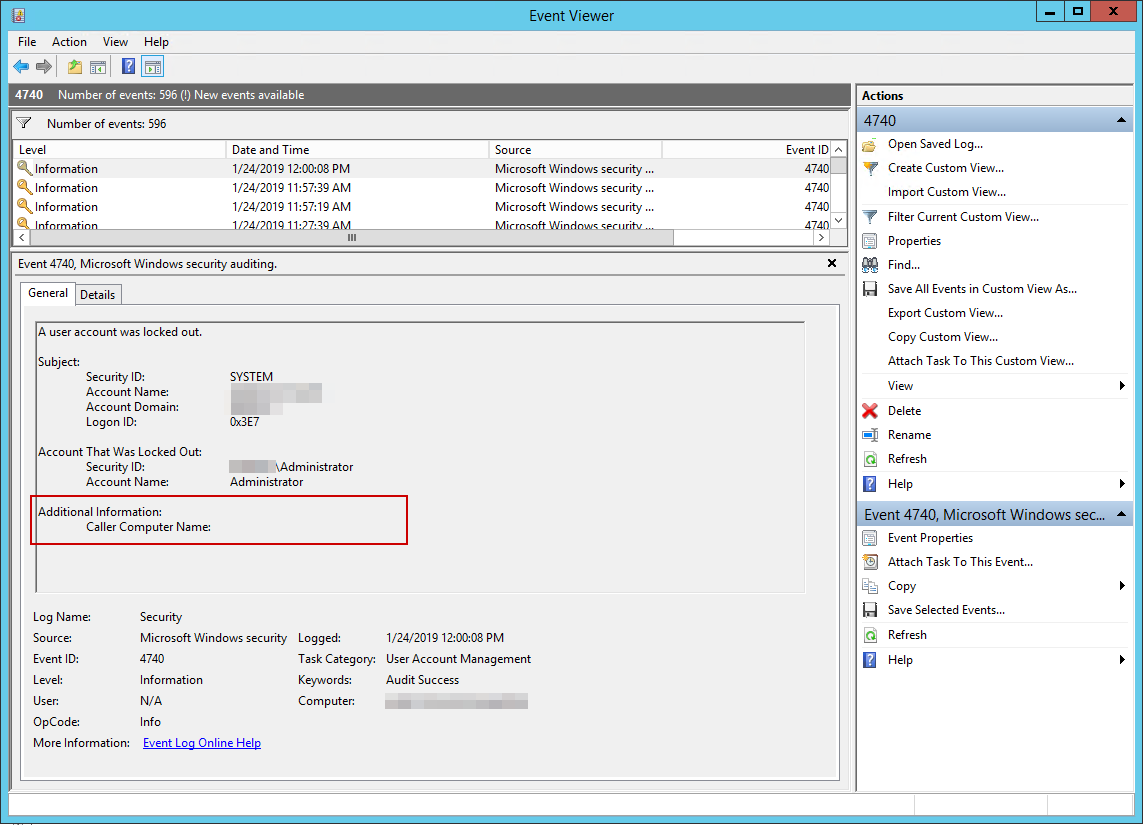
Active Directory – How to track down why and where the user account was locked out
I’ve been working with Windows Events for a while now. One of the things I did to help me diagnose problems and reporting on Windows Events…
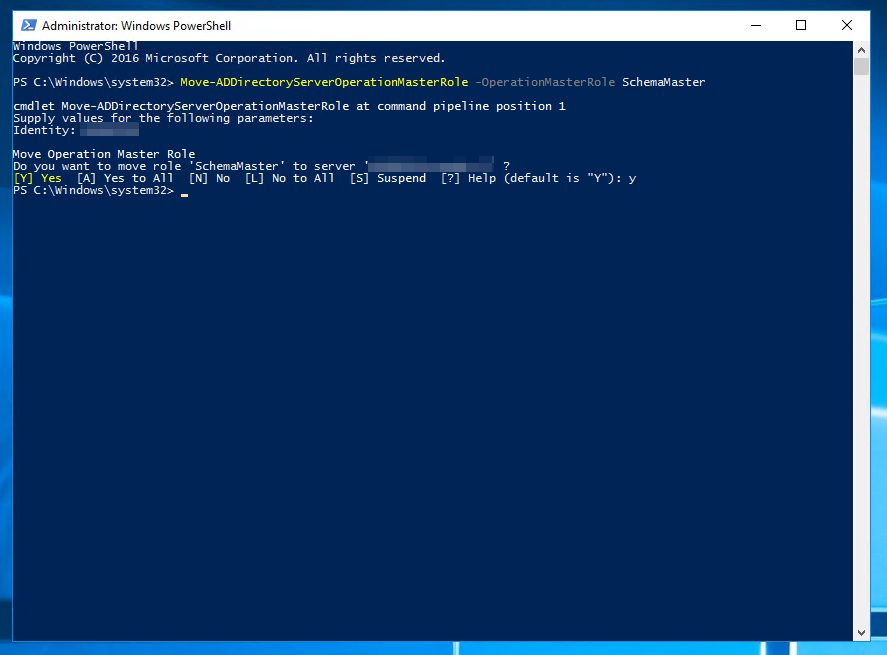
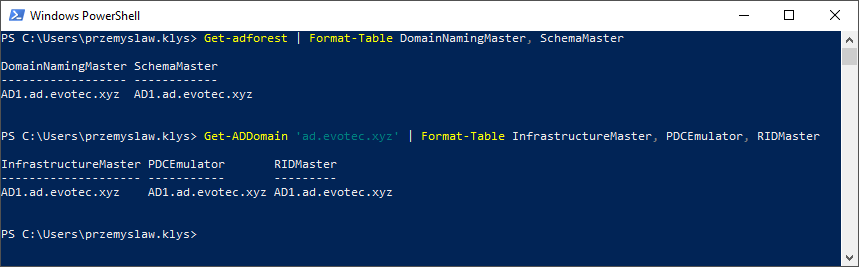
Active Directory – Move-AD Directory Server Operation Master Role: Access is denied
When working with Active Directory one of the common tasks is to move FSMO roles between servers. Well, maybe not that common but it happen…
Active Directory – The directory service was unable to allocate a relative identifier
I’ve been testing Disaster Recovery scenario restoring Active Directory. One of the servers was restored, and it worked for a moment after…
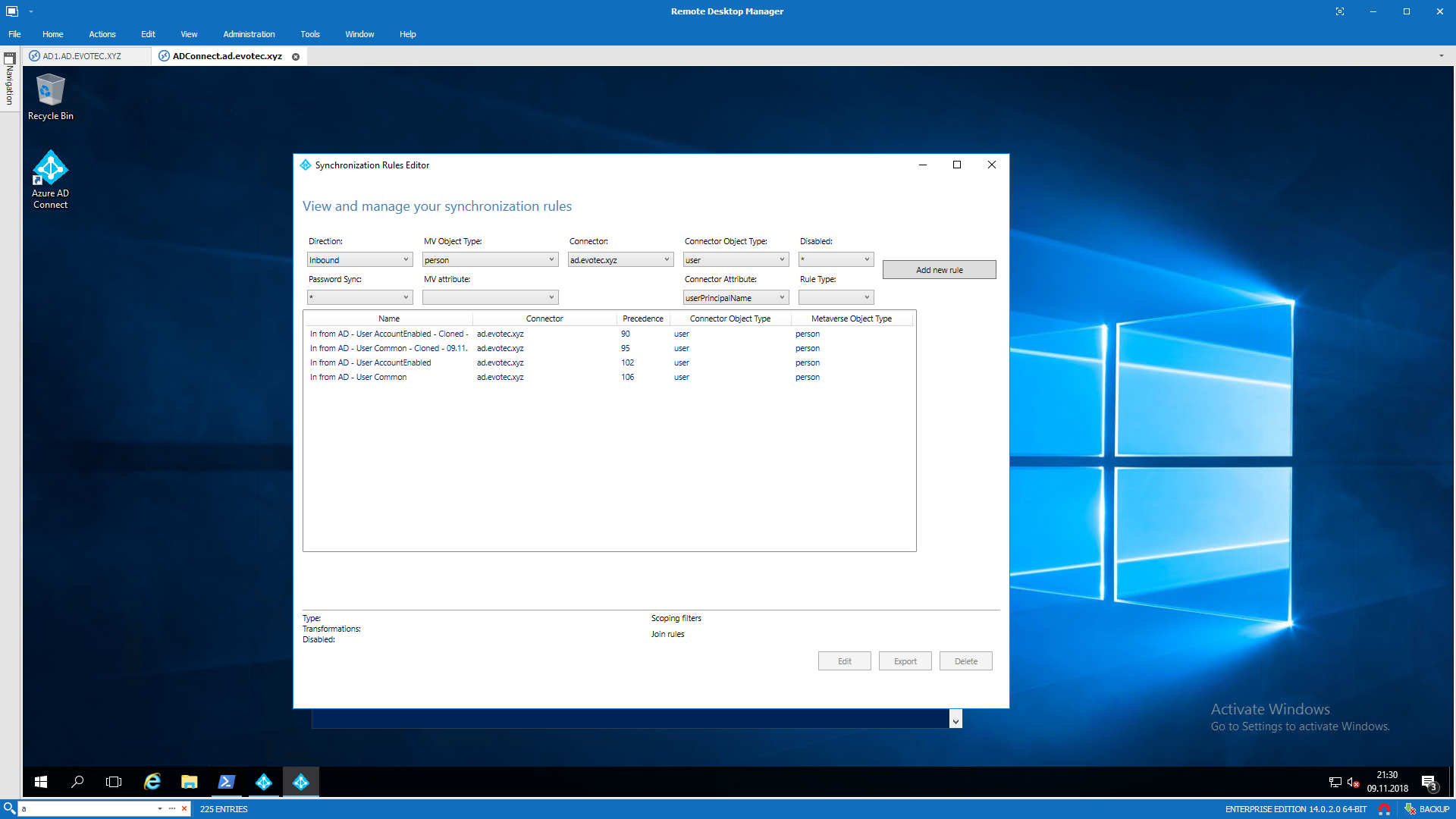
Azure AD Connect – Synchronizing MAIL field with UserPrincipalName in Azure
Azure AD Connect is an application responsible for synchronizing Active Directory with Azure AD allowing for a natural population of users,…

Azure ADConnect Export Failed – Permission-issue error
During our recent setup of Azure ADConnect for one of our Clients we’ve been getting permission-issue – Insufficient access rights…

AzureAD – Enable Password Expiration with Password Hash Synchronization
Enable Office 365 password expiration for Azure AD Connect password hash sync users so cloud sign-ins follow your on-premises policy.
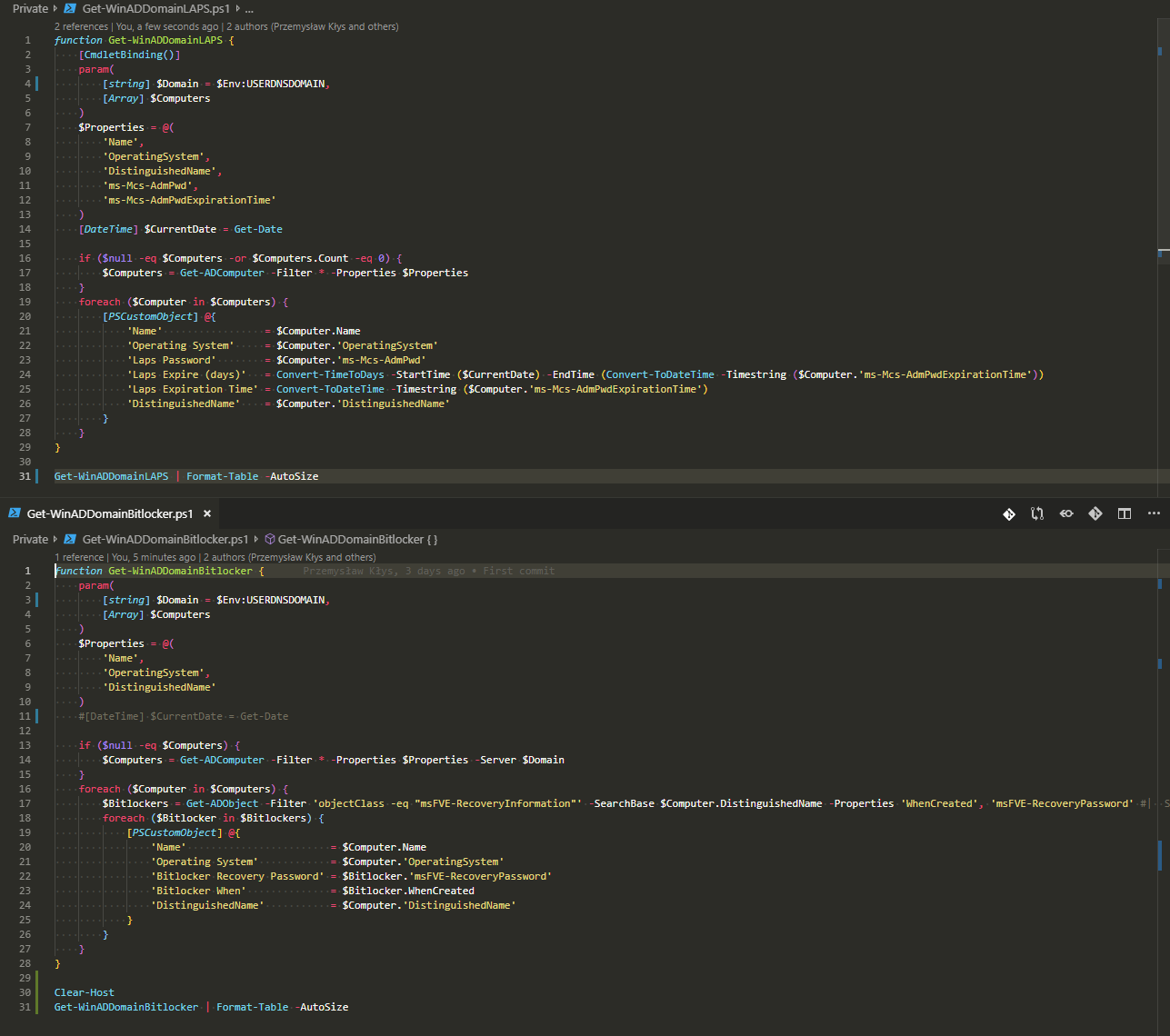
Backing up Bitlocker Keys and LAPS passwords from Active Directory
Back up BitLocker recovery keys and LAPS passwords from Active Directory so older restores and disaster recovery scenarios remain accessibl…

Delegating Active Directory attribute physicalDeliveryOfficeName
Being responsible for Active Directory you’re often tasked with fairly simple task of delegating permissions for user and groups. After…
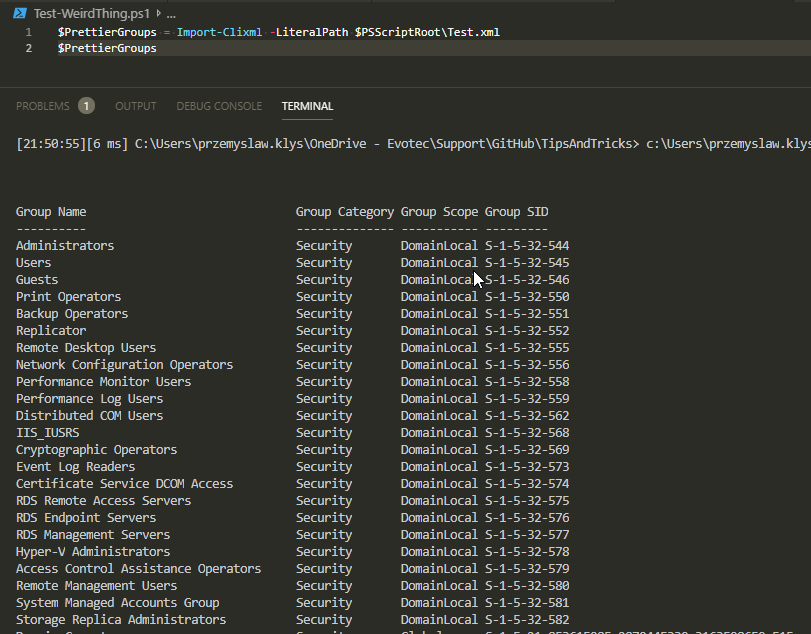
Export-CliXML and Import-CliXML serialization woes
I’ve been working today trying to deliver to one of my Clients Active Directory documentation. To my surprise, something that worked fine f…
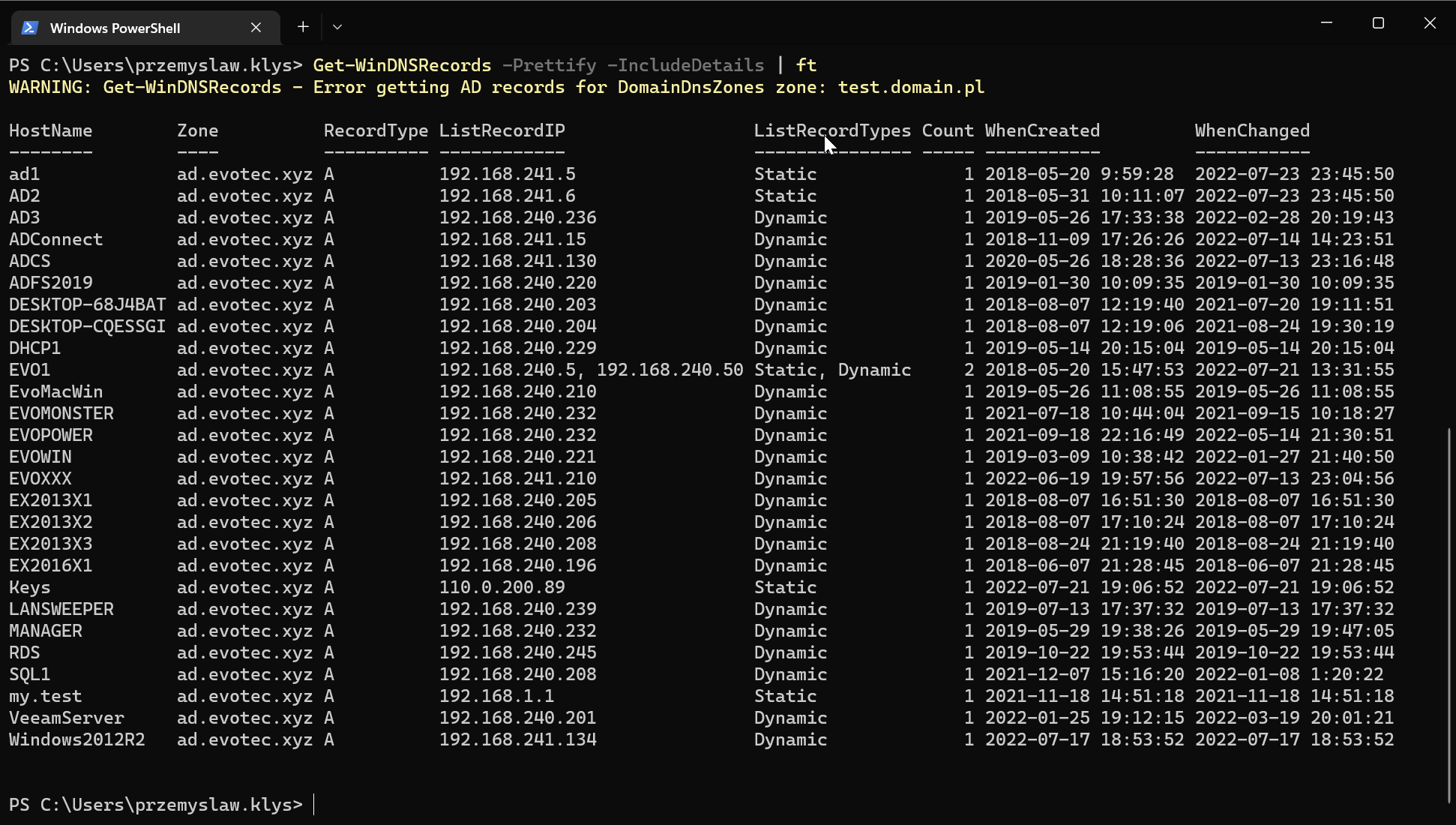
Finding duplicate DNS entries using PowerShell
Today’s blog post is about Active Directory-integrated DNS and how to find duplicate entries. By duplicate, I mean those where one DNS name…
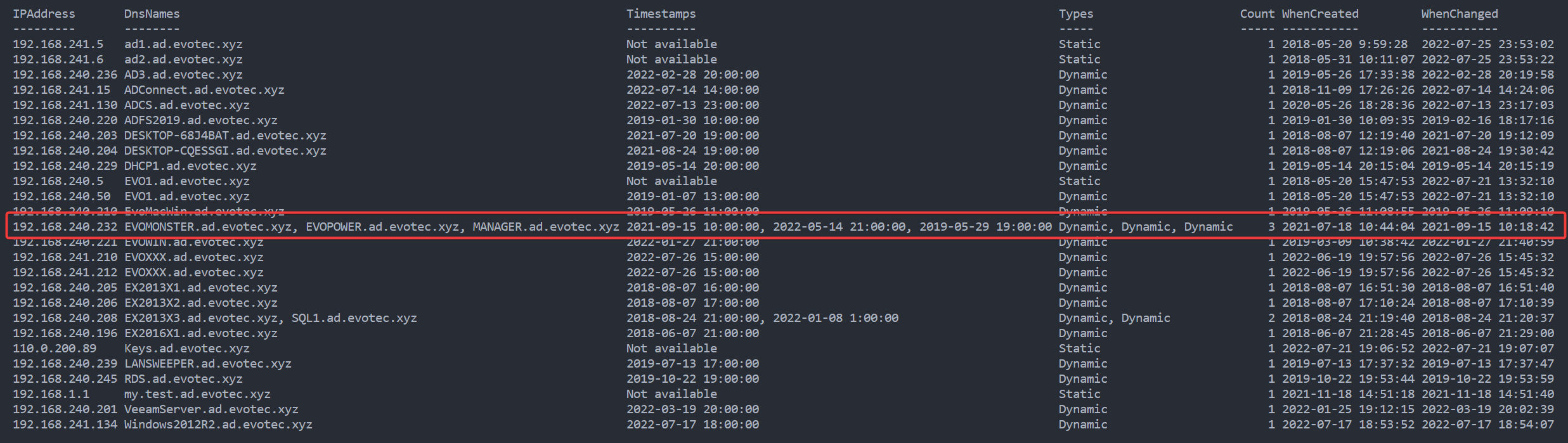
Finding duplicate DNS records by IP Address using PowerShell
In my earlier blog post, I showed you a way to find duplicate DNS entries using PowerShell, but the focus was on finding duplicate entries…
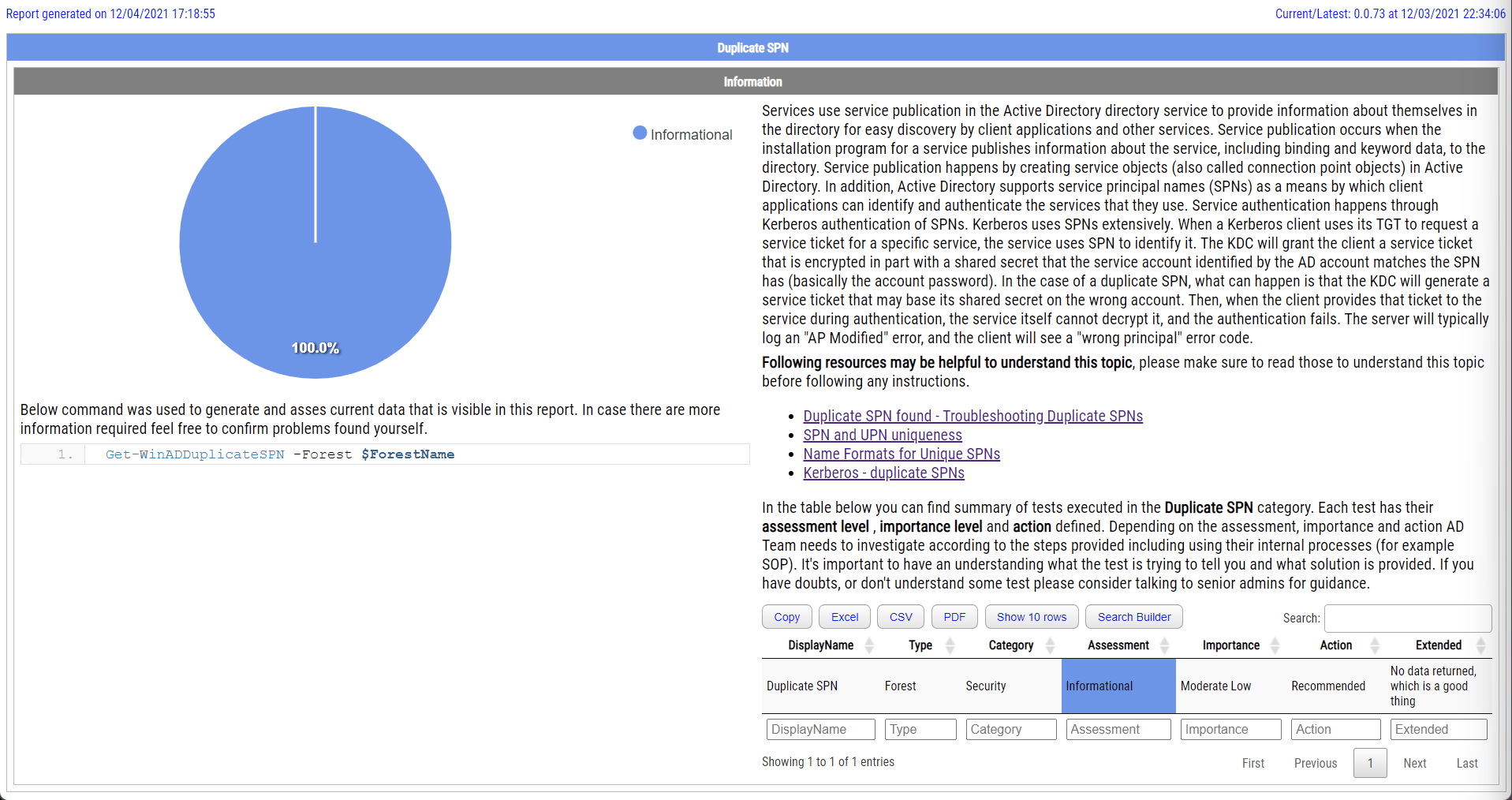
Finding duplicate SPN with PowerShell
Duplicate SPNs aren’t very common but can happen in any Active Directory as there’s no built-in way that tracks and prevent duplicate SPN’s…

Finding GPOs missing permissions that may prevent GPOs from working correctly
I’ve been in IT for a longer time now. I’ve made my fair share of mistakes and misconfigurations. One of those misconfigurations was removi…
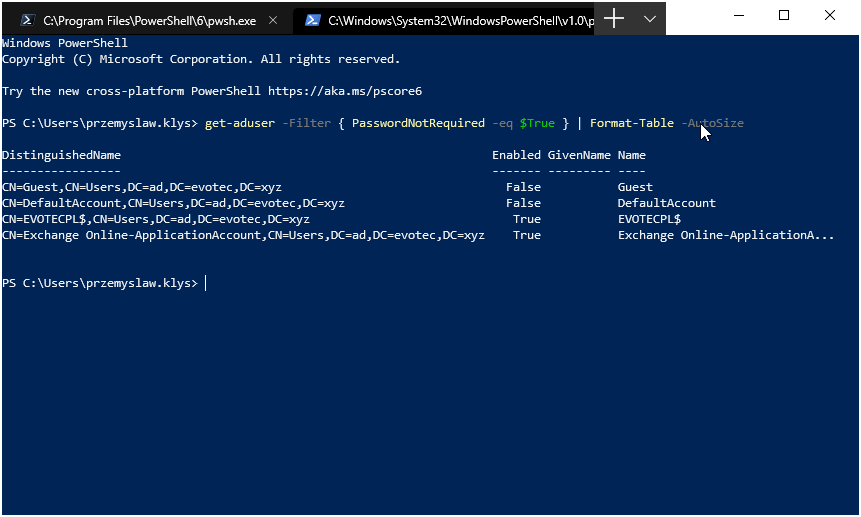
Fixing Active Directory PasswordNotRequired with PowerShell
There was I, deploying PSPasswordExpiryNotifications for one of my Clients when I started getting complaints that some users are not gettin…