categories
Azure
9 entries
9 entries

Accessing AzureVM with NLA and broken domain trust relationship
Regain access to Azure VMs after a broken domain trust by disabling NLA remotely and repairing the machine relationship with PowerShell.

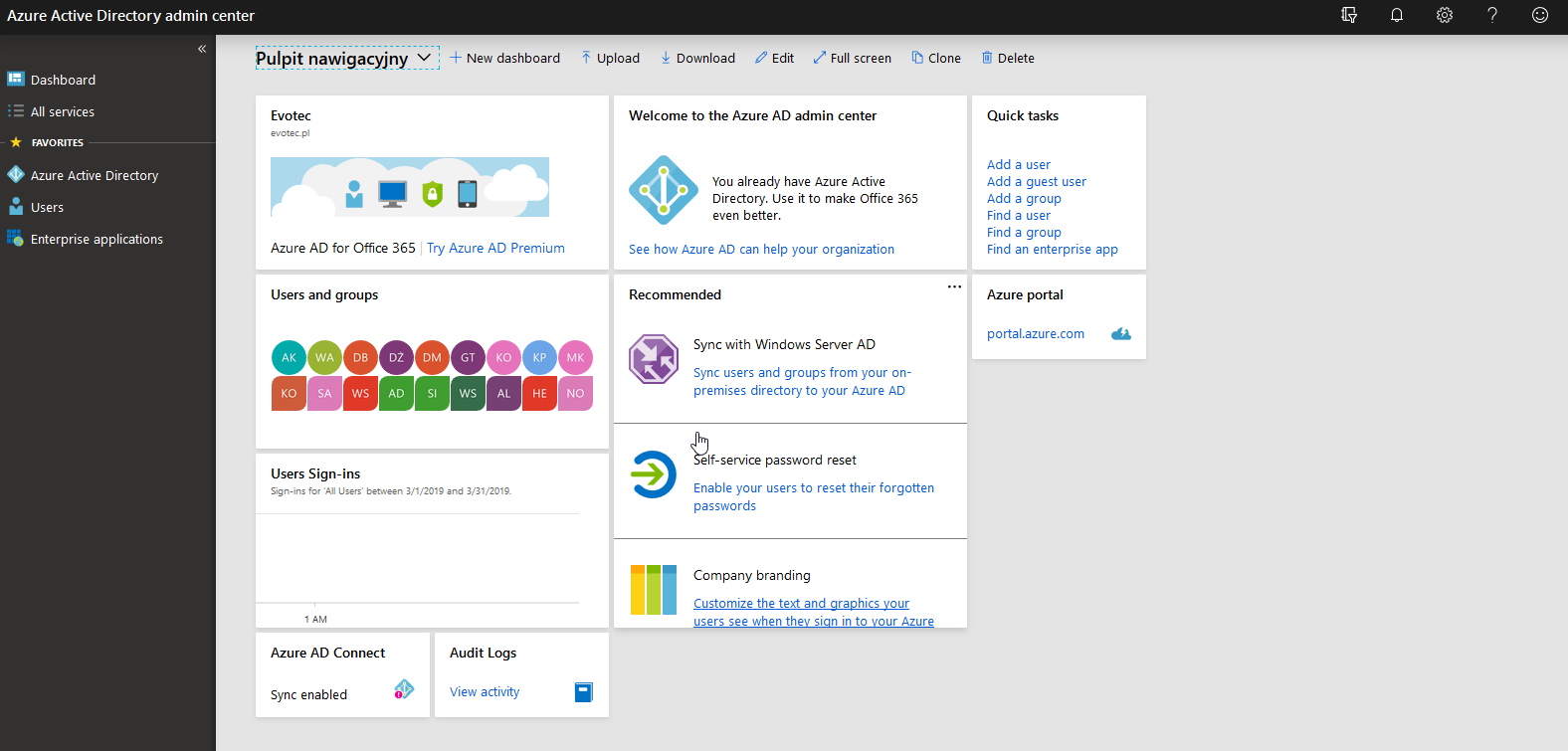
Active Directory Health Check using Microsoft Entra Connect Health Service
Active Directory (AD) is crucial in managing identities and resources within an organization. Ensuring its health is pivotal for the seamle…
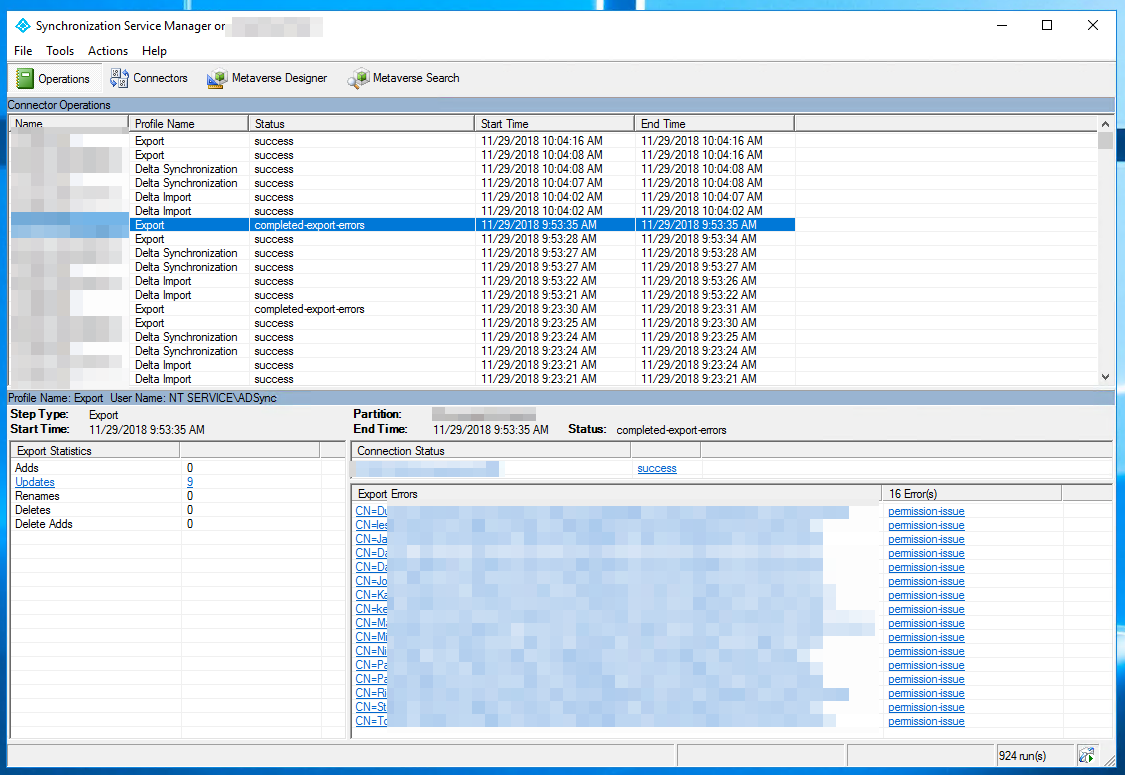
Azure AD Connect – Completed-Export-Errors – Permission-Issue
During synchronization of Active Directory with Office 365 via Azure AD Connect I was greeted with a list of accounts that have permission-…
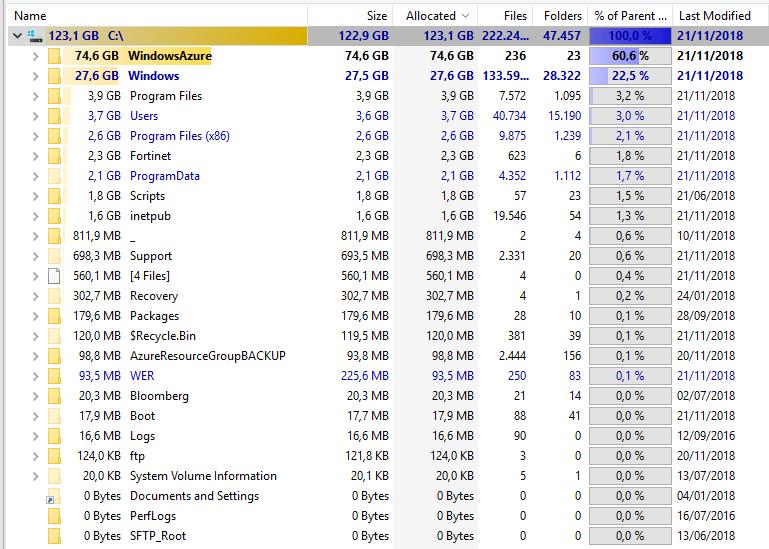
Azure Agent – Where did my space go?
Recently I had a weird case where one of our Azure servers was starting losing space pretty quickly making Pulseway go nuts. As you can ass…

Configuring Office 365 settings using PowerShell – The non-supported way
Use O365Essentials to read and change Microsoft 365 admin settings from PowerShell when the official modules do not expose them.
Free Microsoft Azure/Office365 Fundamentals Training starting February 6th 2023
Being a Microsoft MVP has quite a few benefits. You get to be part of unique offers that help you enhance your knowledge even further. Micr…
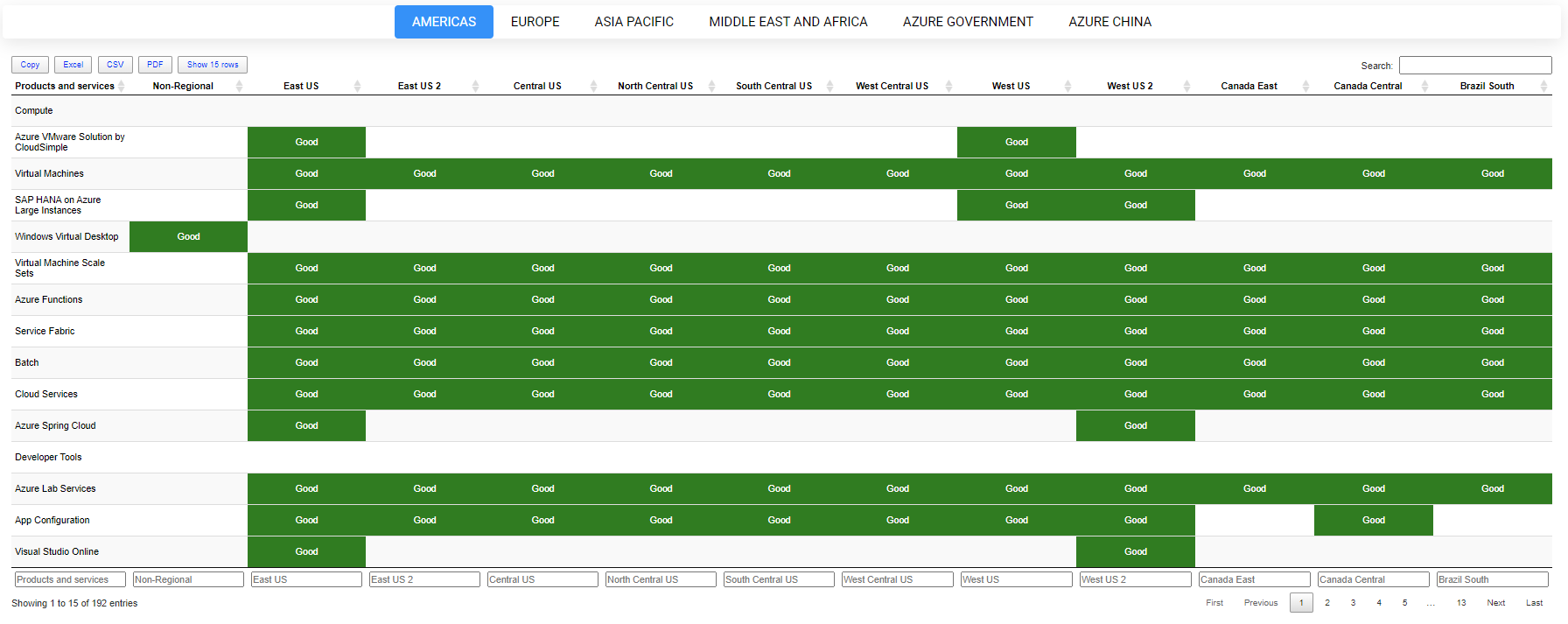
Getting Azure Health by parsing HTML using PSParseHTML
Some time ago I’ve wrote PowerShell way to get all information about Office 365 Service Health, and if you were thinking that I would try t…
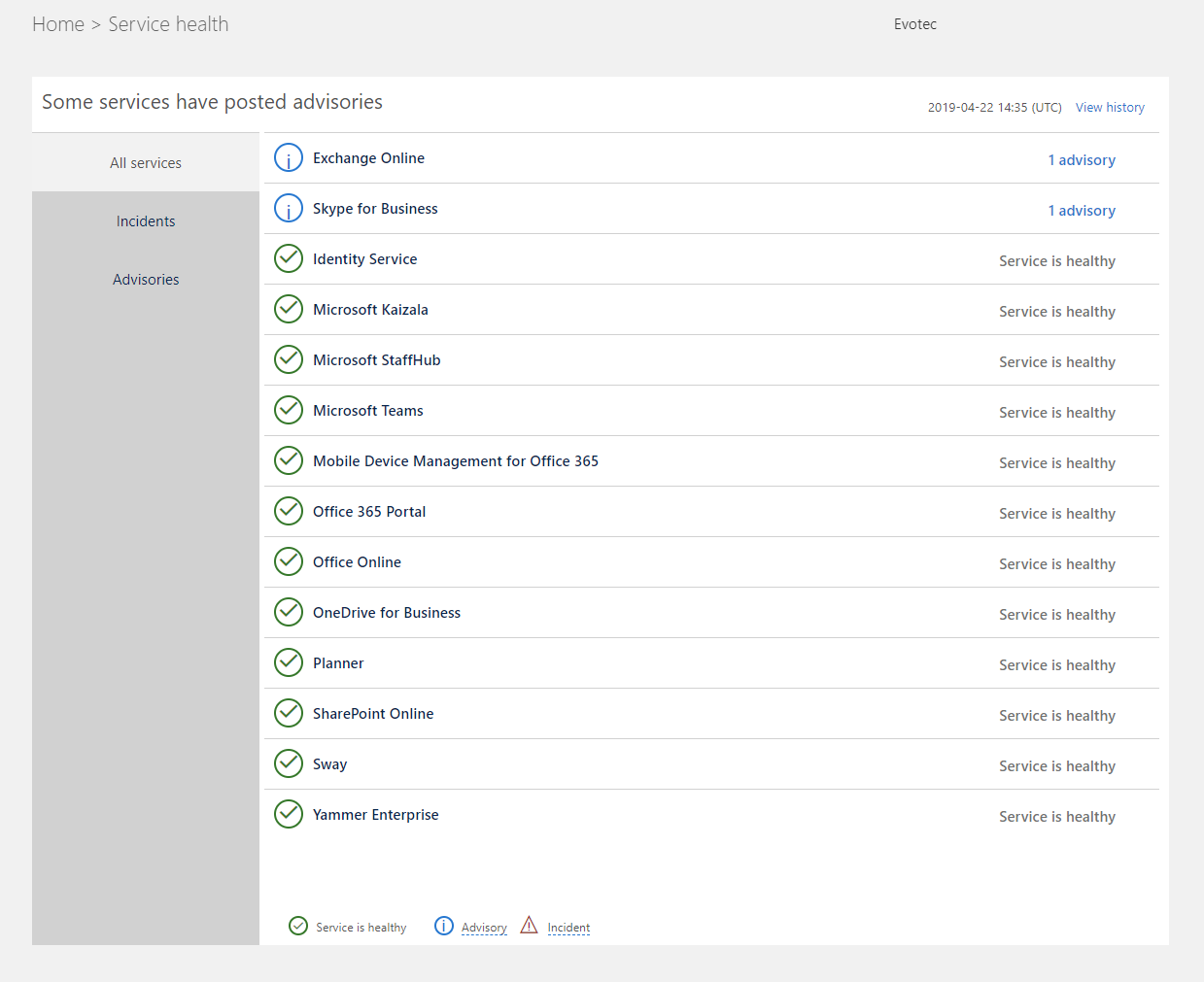
PowerShell way to get all information about Office 365 Service Health
Office 365 is an excellent cloud service. But like any service, there’s some infrastructure behind it that has to be cared for. Since this…
Preparing Azure App Registrations permissions for Office 365 Service Health
As you may have seen in my other post, there’s a simple, PowerShell way to get Office 365 Health Service data for you to use any way you li…