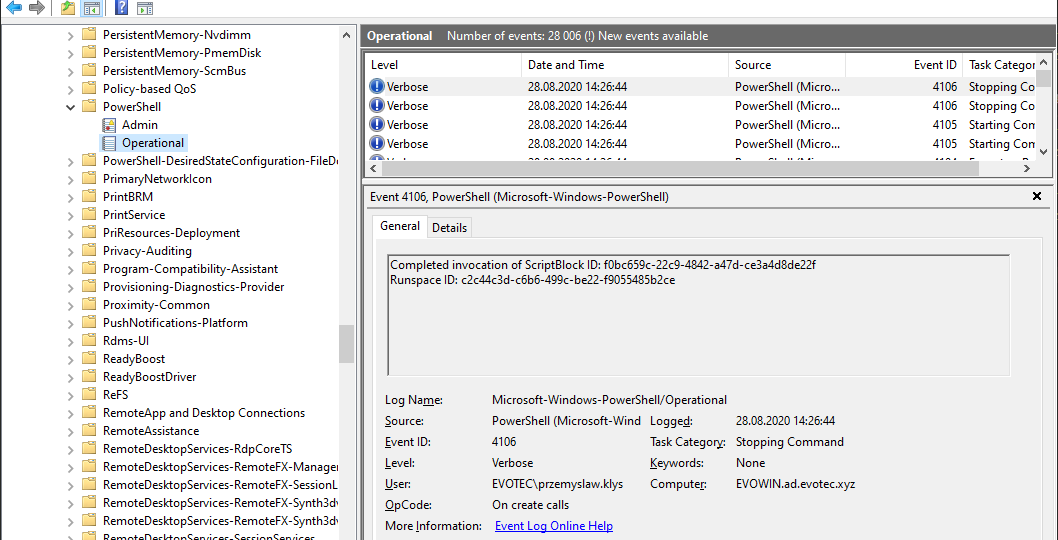
A few days ago, I was asked to take a look at PowerShell Malware. While I don’t know much about malware, my curiosity didn’t let me skip on this occasion, and I was handed over WindowsPowerShell.evtx file. Ok, that’s not what I expected! I wanted PowerShell .ps1 files that I can read and assess? Well, you play with the cards you were dealt with. What I was handed over was PowerShell Event Log. PowerShell writes whatever you execute, and it thinks it is risky, to Windows PowerShell Operation Event Log.
pseventviewer
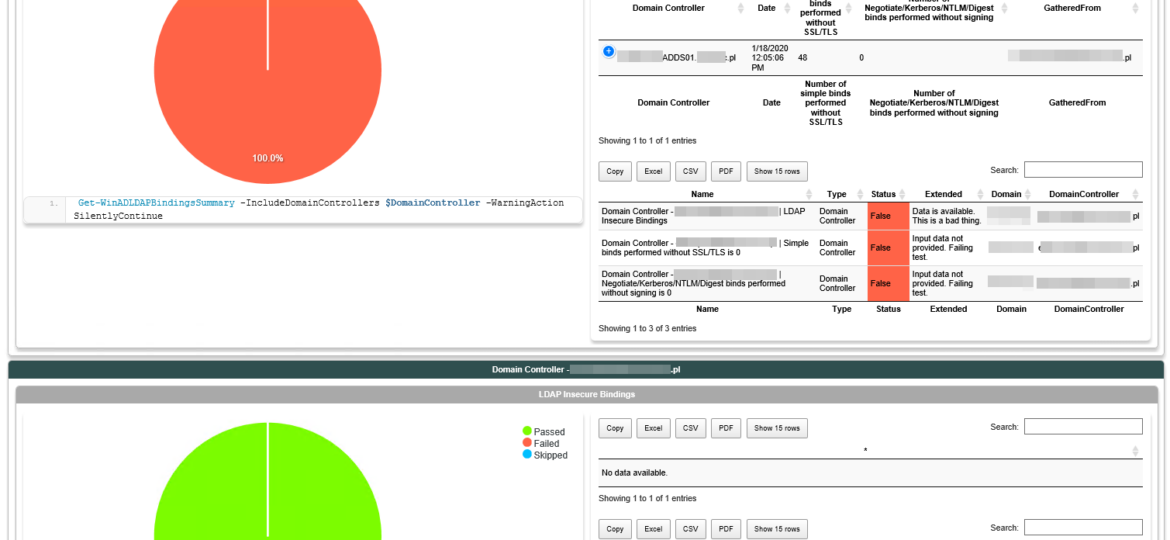
In March 2020, Microsoft will release its monthly updates. With those updates, Microsoft will disable insecure LDAP Bindings, which is going to break a lot of your systems (hopefully not). But this was already communicated, and you know all about it, right? If not, you should read those two articles that can help you with understanding what is happening and when.
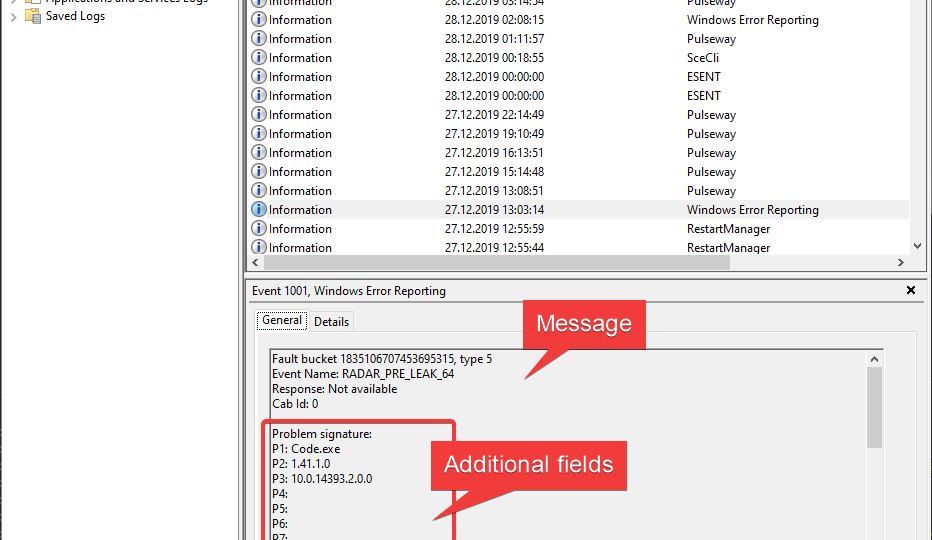
Reading Event Logs is something that every admin does or at least should do quite often. When writing PowerShell scripts, you often need to read event logs to find out different things across your infrastructure. But now and then it’s quite the opposite. You need to write something to Event Log so it can be recorded for the future. Sure, you can write your information to log files, but since Windows already has a built-in logging system, it may be much easier to write stuff to event log. This allows you to centralize your event logs and processed by specialized tools like SIEM.
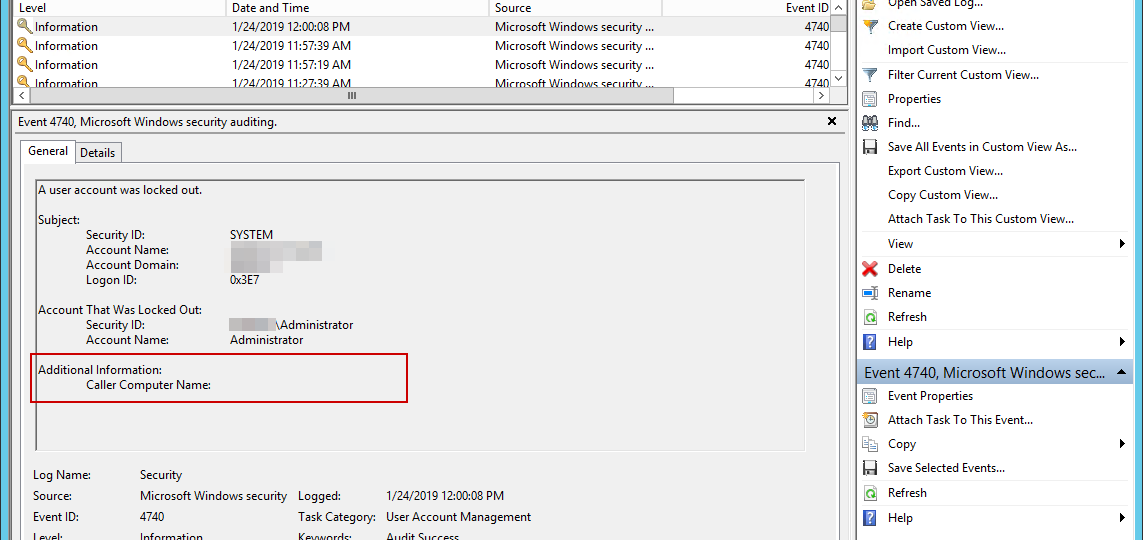
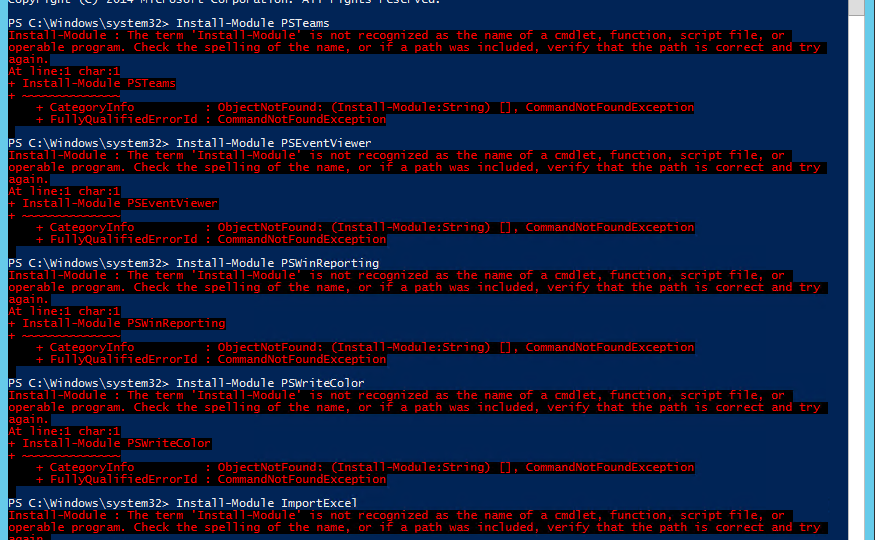
I’ve been working with Windows Events for a while now. One of the things I did to help me diagnose problems and reporting on Windows Events was to write PSEventViewer to help to parse the logs and write PSWinReporting to help monitor (with use of PSEventViewer) Domain Controllers for events that happen across the domain. It’s handy and I, get those excellent daily reports of what happened while I was gone.