tags
powershell
167 entries
20 entries

A command with name is already available on this system. This module may override the existing commands.
Another day, another issue one may say. Today I wanted to install one of my modules to a new server and was greeted with a well-known messa…

Accessing AzureVM with NLA and broken domain trust relationship
Regain access to Azure VMs after a broken domain trust by disabling NLA remotely and repairing the machine relationship with PowerShell.

Active Directory DHCP Report to HTML or EMAIL with zero HTML knowledge
I’m pretty addicted to reading blog posts. I saw this new blog post the other day, where the author created the DHCP HTML report, and he di…

Active Directory Health Check using Microsoft Entra Connect Health Service
Active Directory (AD) is crucial in managing identities and resources within an organization. Ensuring its health is pivotal for the seamle…

Active Directory Replication Summary to your Email or Microsoft Teams
Monitor Active Directory replication with Repadmin summaries delivered to email or Microsoft Teams so failures surface without manual check…
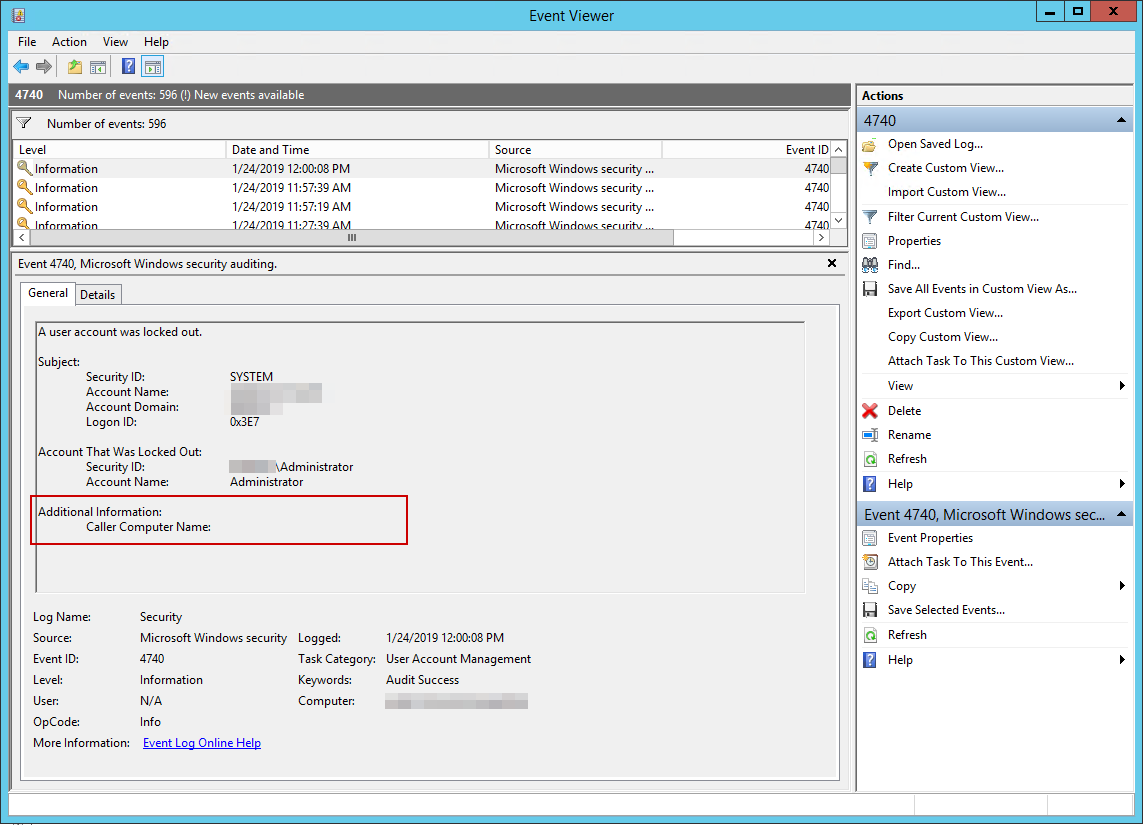
Active Directory – How to track down why and where the user account was locked out
I’ve been working with Windows Events for a while now. One of the things I did to help me diagnose problems and reporting on Windows Events…
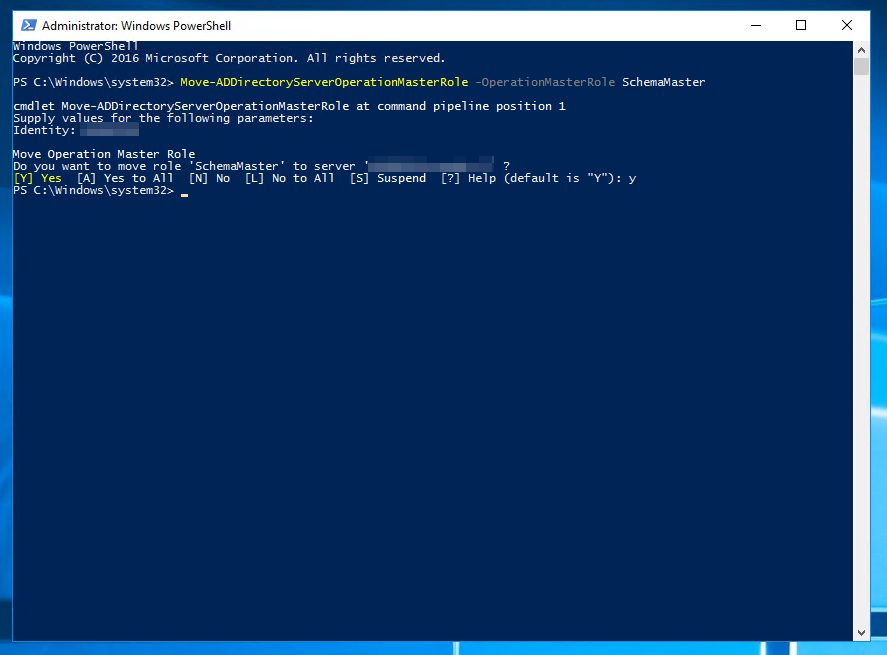
Active Directory – Move-AD Directory Server Operation Master Role: Access is denied
When working with Active Directory one of the common tasks is to move FSMO roles between servers. Well, maybe not that common but it happen…
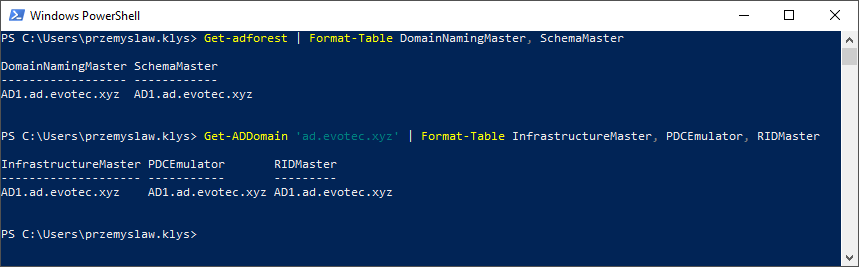
Active Directory – The directory service was unable to allocate a relative identifier
I’ve been testing Disaster Recovery scenario restoring Active Directory. One of the servers was restored, and it worked for a moment after…
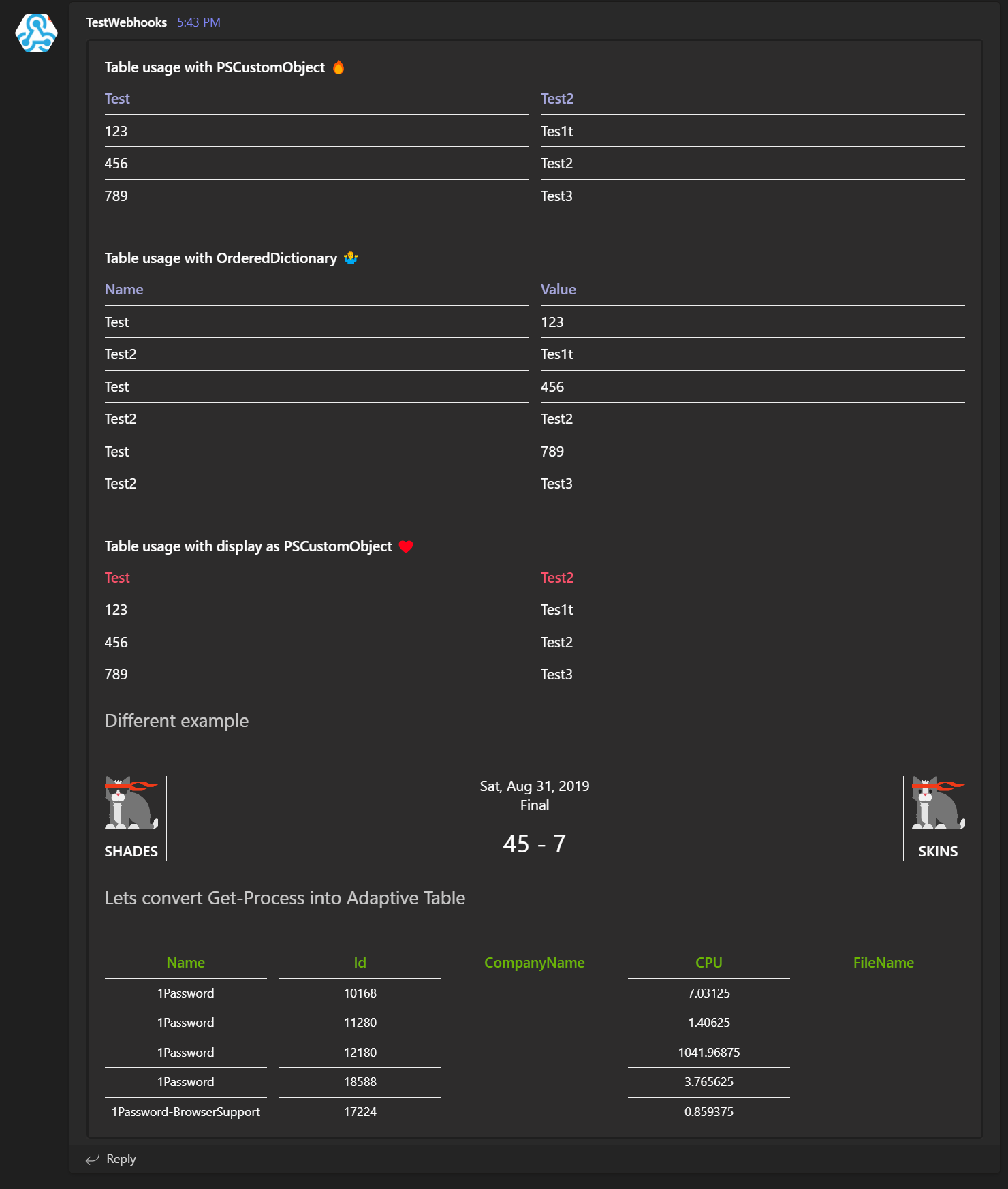
Adaptive Cards with Tables and Linebreaks in Microsoft Teams
PSTeams is a PowerShell module that helps simplify sending notifications to Microsoft Teams via Incoming webhooks. It’s easy to use and doe…

Adding user to local Administrators group in multiple languages
Everyone now and then, there comes a moment you need to add a user into Administrators group on each computer…
Advanced HTML reporting using PowerShell
I’ve been using HTML reporting in PowerShell for a while. Initially, I would usually build HTML by hand, but the time spent trying to figur…

All your HTML Tables are belong to us
Build complex HTML tables from PowerShell with PSWriteHTML, including multi-row headers and report layouts that are painful to hand-code.

Azure ADConnect Export Failed – Permission-issue error
During our recent setup of Azure ADConnect for one of our Clients we’ve been getting permission-issue – Insufficient access rights…

AzureAD – Enable Password Expiration with Password Hash Synchronization
Enable Office 365 password expiration for Azure AD Connect password hash sync users so cloud sign-ins follow your on-premises policy.
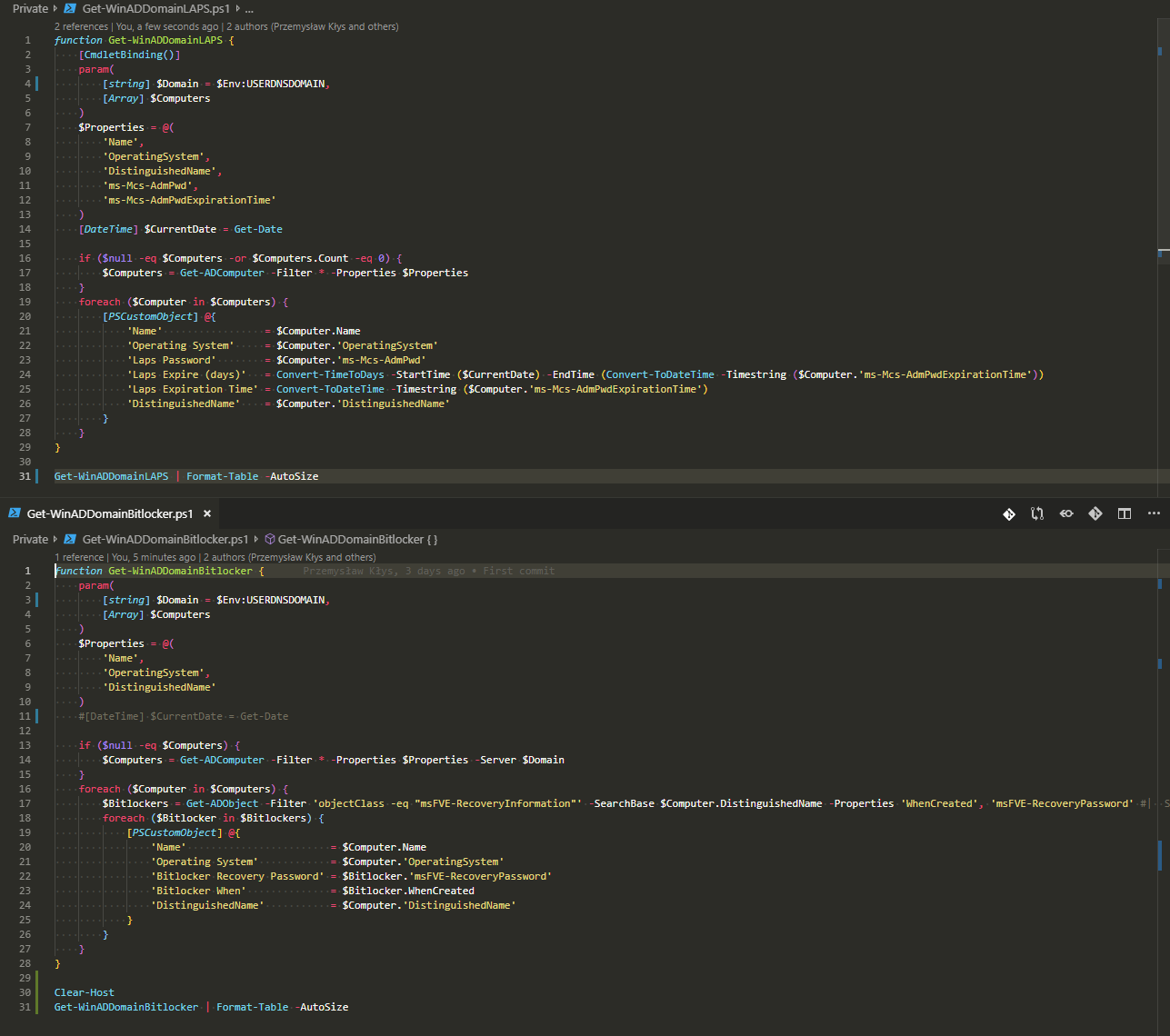
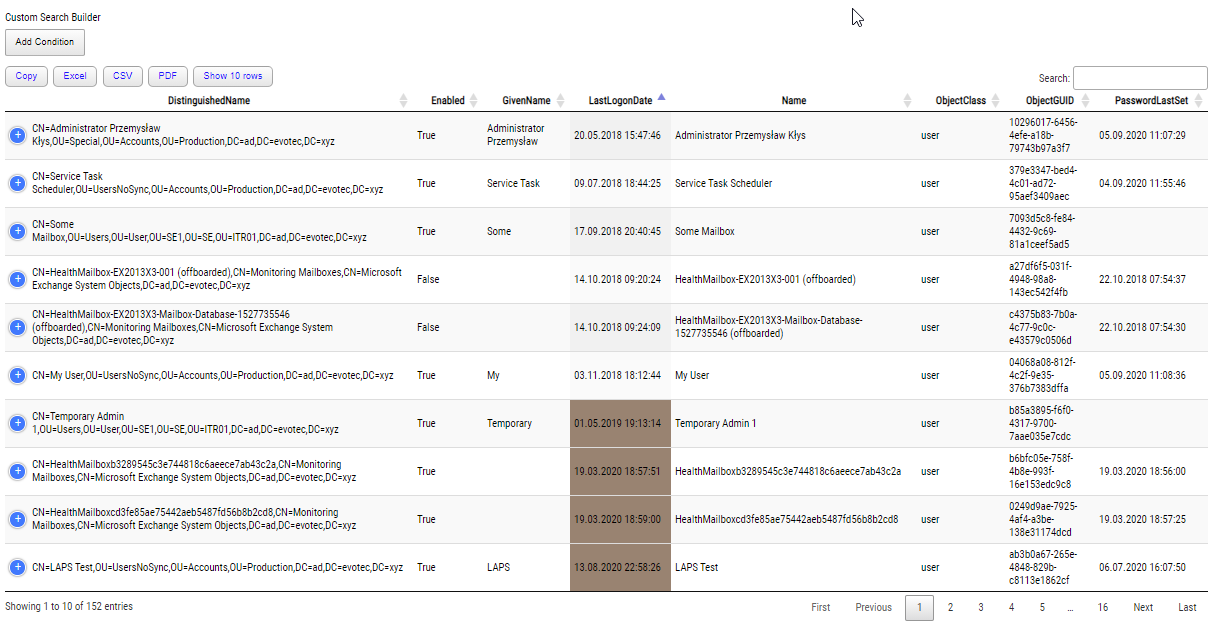
Backing up Bitlocker Keys and LAPS passwords from Active Directory
Back up BitLocker recovery keys and LAPS passwords from Active Directory so older restores and disaster recovery scenarios remain accessibl…

Changing Exchange folder permissions in multilanguage Office 365 tenants
One of the tasks I often get when setting up new Office 365 tenant or installing Exchange Servers is to change the visibility of Room Mailb…

Comparing two or more objects visually in PowerShell (cross-platform)
Compare two or more PowerShell objects visually with PSWriteHTML so property differences are easier to review, share, and export.

Configuring Office 365 settings using PowerShell – The non-supported way
Use O365Essentials to read and change Microsoft 365 admin settings from PowerShell when the official modules do not expose them.
Connect-MgGraph: Keyset does not exist
If Connect-MgGraph works interactively but fails in a scheduled task with 'Keyset does not exist', the certificate is usually installed in…

Converting Pester V4 to Pester V5 basics
Convert Pester v4 tests to Pester v5 basics, understand the breaking changes, and get existing PowerShell test suites running again faster.