tags
azure ad
12 entries
12 entries

Active Directory Health Check using Microsoft Entra Connect Health Service
Active Directory (AD) is crucial in managing identities and resources within an organization. Ensuring its health is pivotal for the seamle…
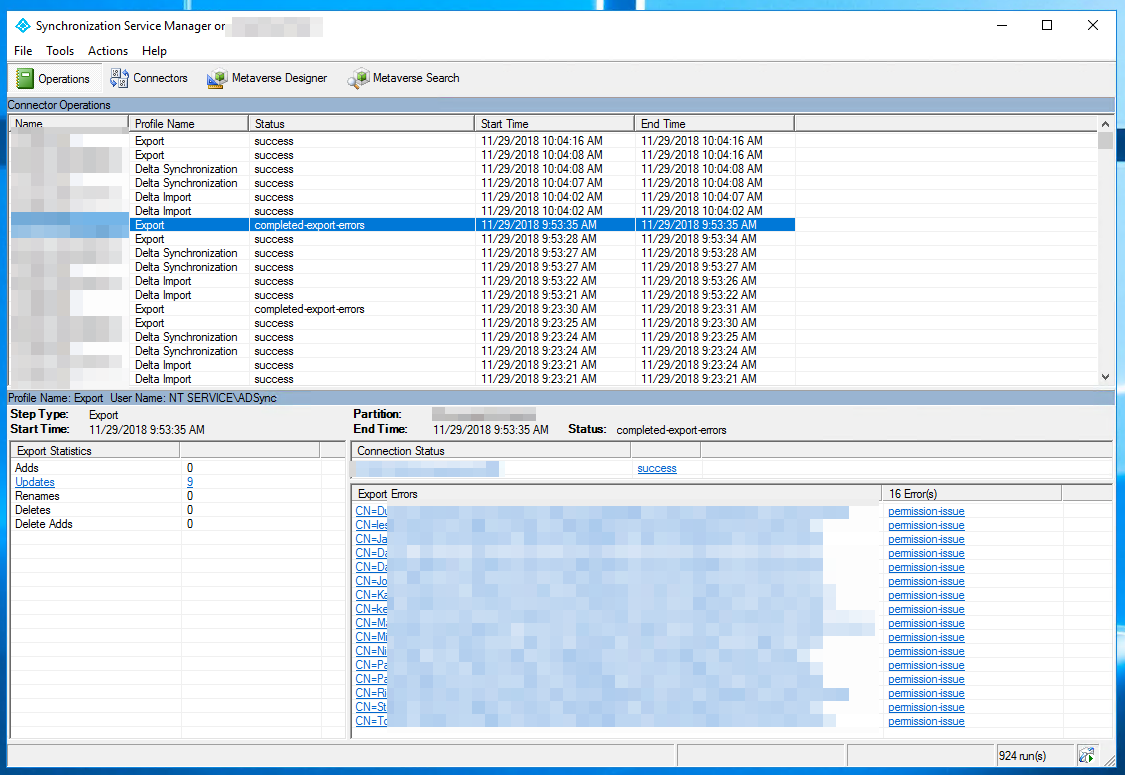
Azure AD Connect – Completed-Export-Errors – Permission-Issue
During synchronization of Active Directory with Office 365 via Azure AD Connect I was greeted with a list of accounts that have permission-…
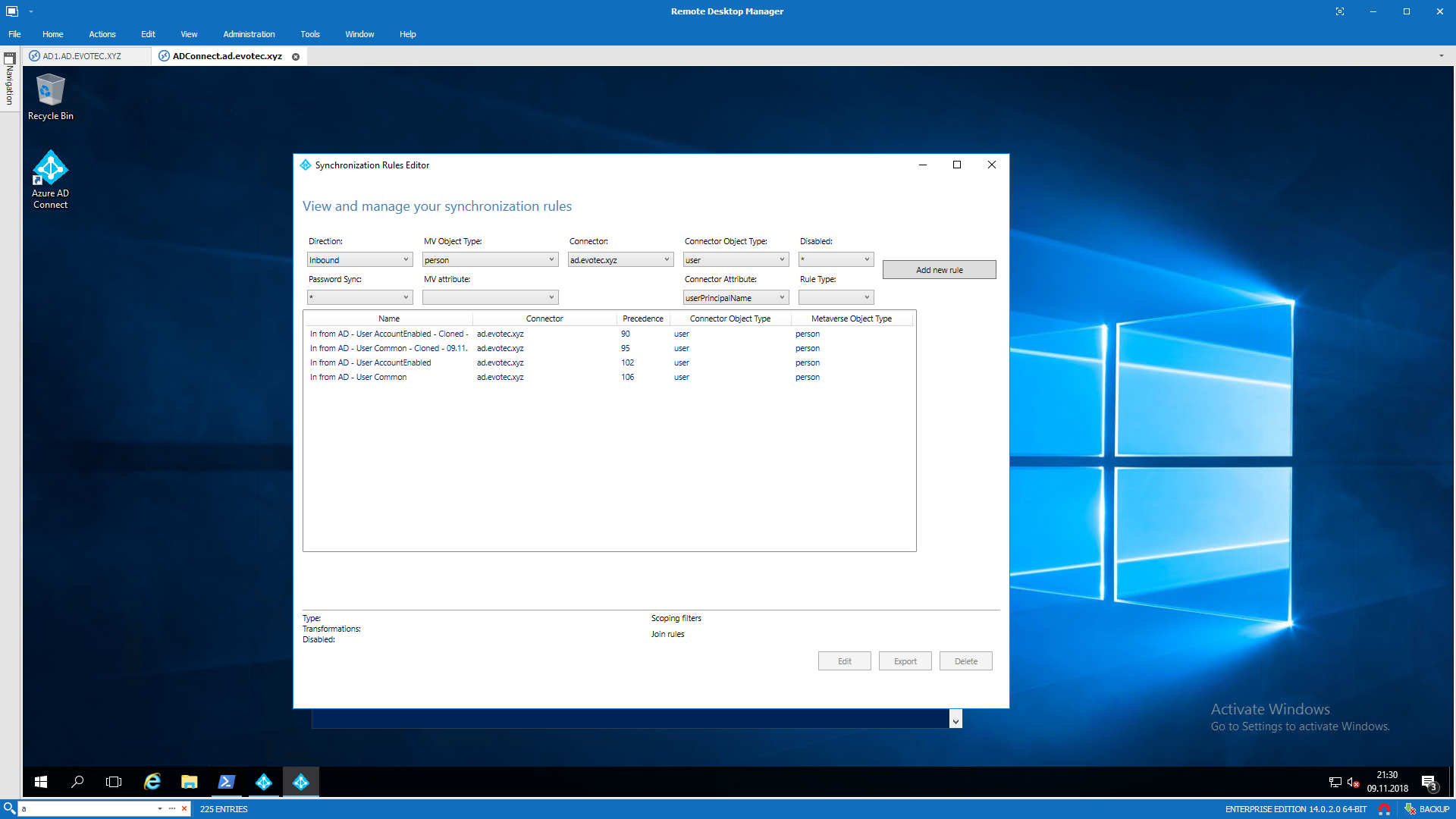
Azure AD Connect – Synchronizing MAIL field with UserPrincipalName in Azure
Azure AD Connect is an application responsible for synchronizing Active Directory with Azure AD allowing for a natural population of users,…
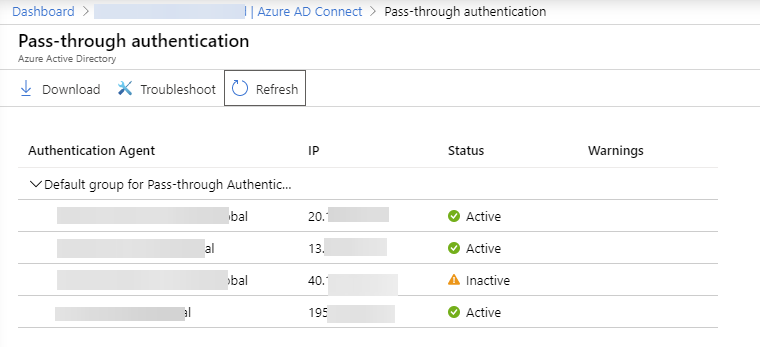
Azure AD – Removing Inactive Azure AD Pass-through Agent
Recently I was switching Office 365 tenant from ADFS to Azure AD Pass-through authentication (PTA). It all went smoothly with one exception…

Azure ADConnect Export Failed – Permission-issue error
During our recent setup of Azure ADConnect for one of our Clients we’ve been getting permission-issue – Insufficient access rights…

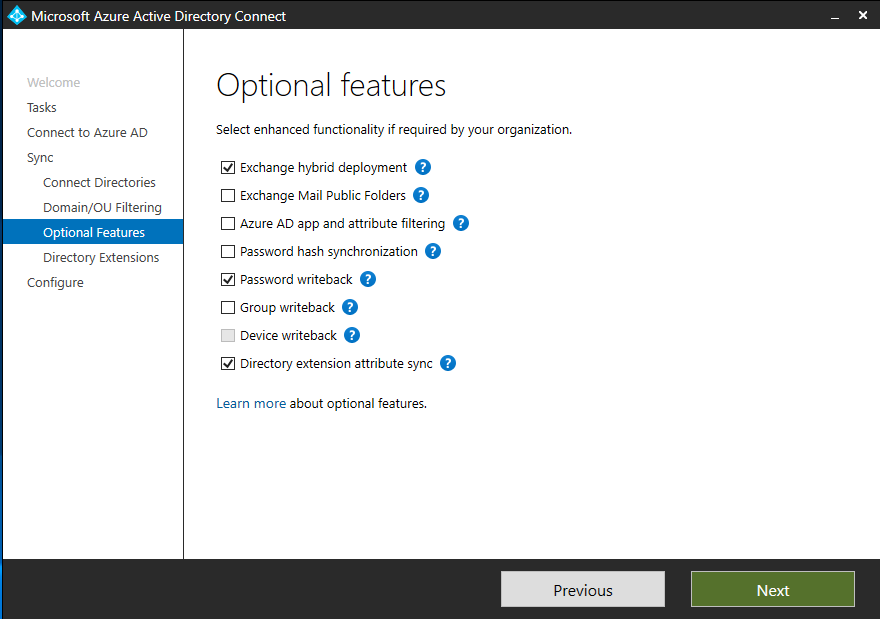
AzureAD – Enable Password Expiration with Password Hash Synchronization
Enable Office 365 password expiration for Azure AD Connect password hash sync users so cloud sign-ins follow your on-premises policy.
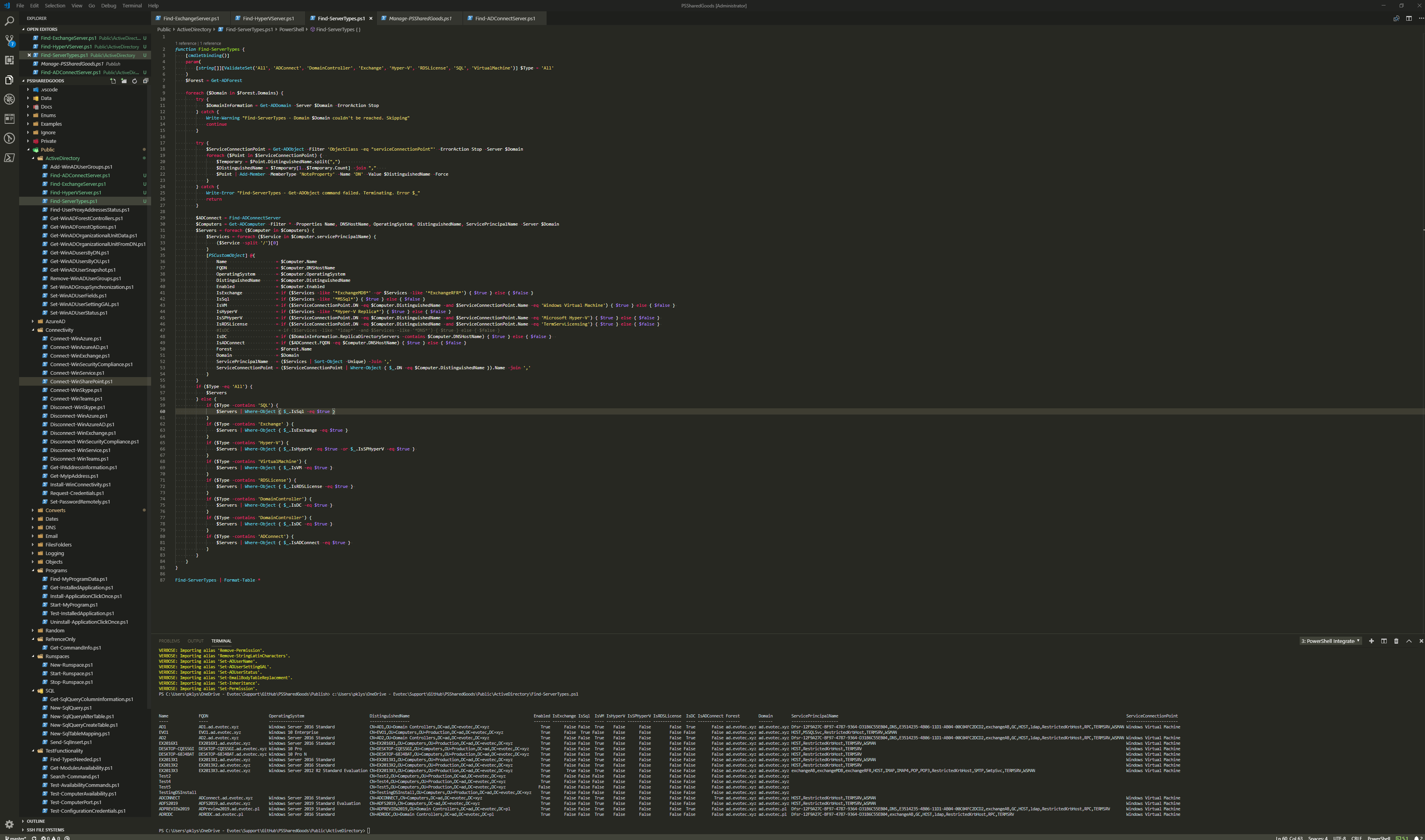
How to find different server types in Active Directory with PowerShell
Working as a freelancer is a great thing if you can handle it. Each day, each week something new happens and a new problem shows up on my d…
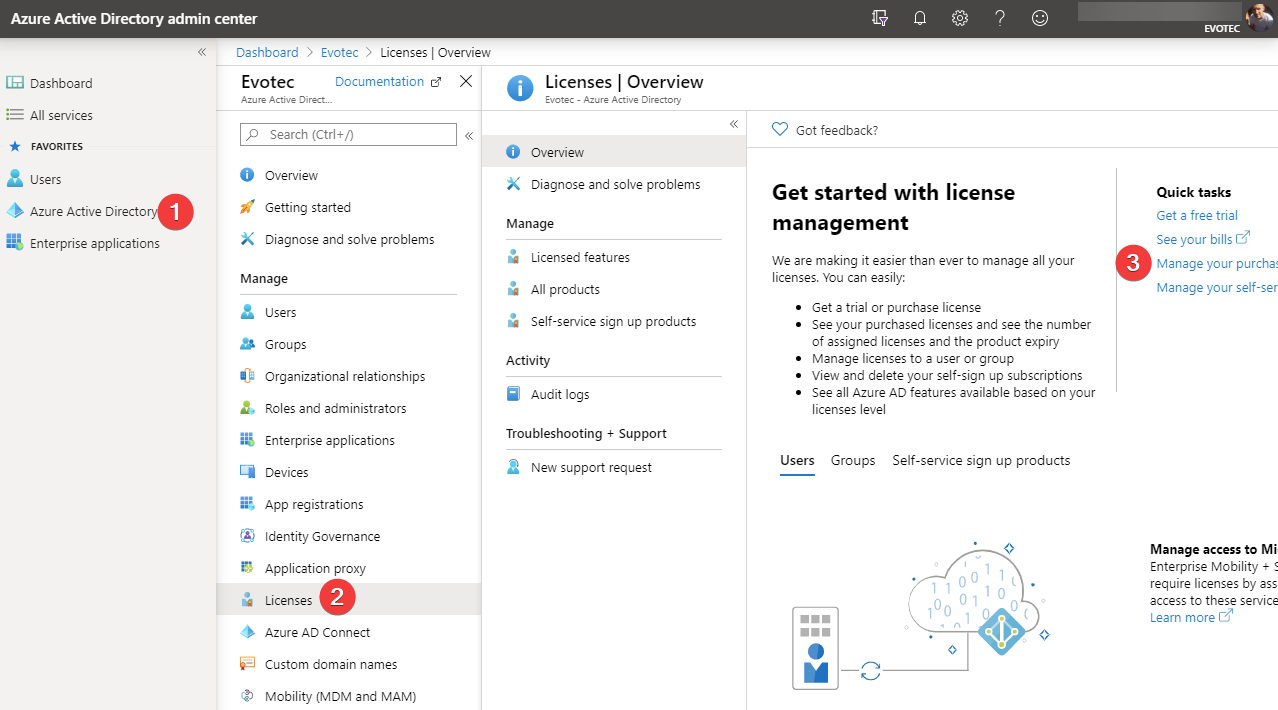
Office 365 – Limiting license to minimum apps required
Office 365 has a lot of options and applications to choose from. Enabling one E1, E3, or any other license gives the user a lot of features…
Office 365 – msExchHideFromAddressLists does not synchronize with Office 365
In my life I’ve deployed multiple Office 365 tenants connected with Active Directory and I’ve been synchronizing msExchHideFromAddressLists…
Report Active Directory Accounts that are Synchronized with Azure AD
I was scrolling X (aka Twitter) today and saw this blog post, “PowerShell: Report On-Premises Active Directory Accounts that are Synchroniz…
Upgrade Azure Active Directory Connect fails with unexpected error
Today, I made the decision to upgrade my test environment and update the version of Azure AD Connect to the latest one. The process is usua…
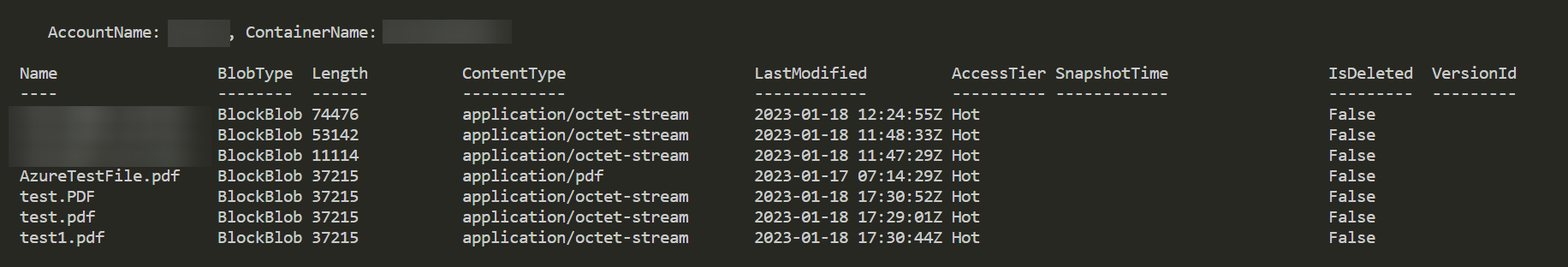
Upload and Download files from Azure Blob Storage using Connection String
They say there is a first time for everything. For me, it’s how to download and upload files to Azure Blog Storage using Connection String.…