Everyone now and then, there comes a moment you need to add a user into Administrators group on each computer in domain. It's not a big problem, if all your systems are in one language, or if you have to just add one user to multiple systems which you can easily accomplish with Group Policies. It gets a bit harder if you need to add one user per machine, and even harder if you need to add one user per machine with unknown language.
There are different approaches to this problem and many batch and powershell solutions. One of those approaches is to get the Administrators group name in multiple languages and simply code it in. The other approach which we describe below is to use Domain Admins name which is consistent across the domain and is based on language name of domain controller rather than on system it's used on. We simply scan all local groups for the standard Domain Admins group which should only be available in local Administrators group on local machine, and when that group is found we add the user inside without checking the rest of the groups. It's not the fastest solution but it surely gets the job done without knowing all the Administrators group names in all languages, and additionally you can always use it for different purposes. The last approach described in here is the fastest one and it's using Well-Known-SIDs allowing to add user directly to the group without knowing it's name.
1⃣ First approach
If you're into old approach (multiply this per each language changing Administrators to respective group names):
net localgroup Administrators Evotec\user1 /add
2⃣ Second approach
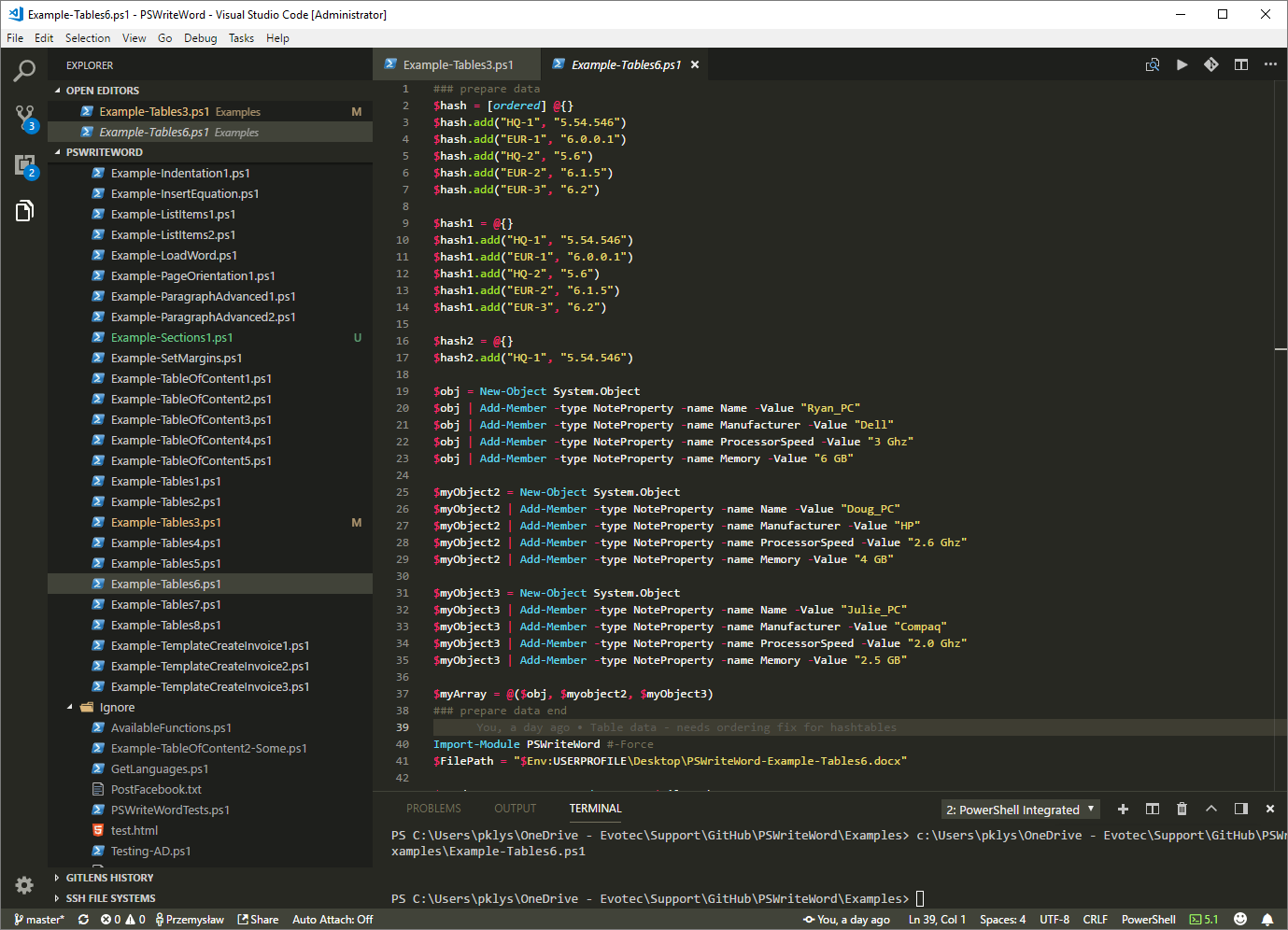
If you would like to go with approach of finding Domain Admins first and then adding a user you can simply use this code:
$gComputerName = $env:COMPUTERNAME # Computer to ADD user to
$gLookFor = "Administratorzy domeny" # Domain Admins group for Domain Controller in Polish Language
$gDomain = "Evotec" # Domain Name
$gUser = "user1" # UserName to ADD
function DoWork($computerName, $groupToLookFor, $domain, $user) {
cls
$groups = get-wmiobject -Query "select * from Win32_Group Where Domain='$computerName'" -ComputerName $computerName
Foreach ($group in $($groups.Name)) {
Write-Host "Checking group $group" -ForegroundColor Magenta
$members = (Get-LocalGroupMembers -ComputerName $computerName -GroupName $group).Members
foreach ($member in $members) {
if ($member -eq $groupToLookFor) {
Write-Host "Found $member" -ForegroundColor Magenta
Write-Host "Adding User $gDomain\$gUser " -ForegroundColor Magenta
Set-User $computerName $group $domain $user
Write-Host "Quitting. My job is done." -ForegroundColor Magenta
exit
}
}
}
}
function Set-User ($computer, $group, $domain, $user) {
try {
$de = [ADSI]"WinNT://$computer/$Group,group"
$de.psbase.Invoke("Add",([ADSI]"WinNT://$domain/$user").path)
} catch {
write-host "User not added, already exists or not running as Administrator" -ForegroundColor Red
}
}
function Get-LocalGroupMembers {
param(
[parameter(Mandatory=$true,ValueFromPipeline=$true,ValueFromPipelineByPropertyName=$true)]
[Alias("Name")]
[string]$ComputerName,
[string]$GroupName = "Administrators"
)
begin {}
process
{
# If the account name of the computer object was passed in, it will
# end with a $. Get rid of it so it doesn't screw up the WMI query.
$ComputerName = $ComputerName.Replace("`$", '')
# Initialize an array to hold the results of our query.
$arr = @()
$wmi = Get-WmiObject -ComputerName $ComputerName -Query ` "SELECT * FROM Win32_GroupUser WHERE GroupComponent=`"Win32_Group.Domain='$ComputerName',Name='$GroupName'`""
# Parse out the username from each result and append it to the array.
if ($wmi -ne $null)
{
foreach ($item in $wmi)
{
$arr += ($item.PartComponent.Substring($item.PartComponent.IndexOf(',') + 1).Replace('Name=', '').Replace("`"", ''))
}
}
$hash = @{ComputerName=$ComputerName;Members=$arr}
return $hash
}
end{}
}
DoWork $gComputerName $gLookFor $gDomain $gUser
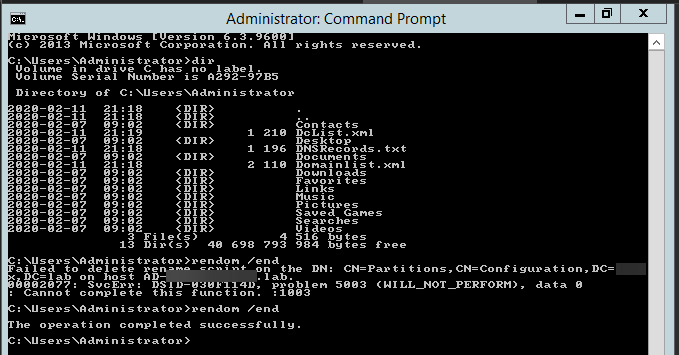
The output of the script is pretty simple. When run first time:
Checking group Access Control Assistance Operators Checking group Administrators Found Administratorzy domeny Adding User Evotec\user1 Quitting. My job is done.
The output of the script when run 2nd time on same machine where user already exists:
Checking group Access Control Assistance Operators Checking group Administrators Found Administratorzy domeny Adding User Evotec\user1 User not added, already exists or not running as Administrator Quitting. My job is done.
As there's not much error checking being done on each level and you're little paranoid you can always add more protection. Of course if you would like to deploy this script to multiple computers and different computer requires different user some modifications are required for this scenario.
3⃣ Third approach
Our final approach by finding SID of the group (below is a list of all well known SIDs just in case you need one.
$gComputerName = $env:COMPUTERNAME # Computer to ADD user to
$gLookForBySid = "S-1-5-32-569" # group sid Cryptographic Operators
$gDomain = "Evotec" # Domain Name
$gUser = "user1" # UserName to ADD
function DoWork($computerName, $groupSidToLookFor, $domain, $user) {
cls
Write-Host "Checking group SID $groupSidToLookFor" -ForegroundColor Magenta
$group = Get-GroupBySid $computerName $groupSidToLookFor
Write-Host "Adding User $gDomain\$gUser to group $group" -ForegroundColor Magenta
Set-User $computerName $group $domain $user
Write-Host "Quitting. My job is done." -ForegroundColor Magenta
exit
}
function Set-User ($computer, $group, $domain, $user) {
try {
$de = [ADSI]"WinNT://$computer/$Group,group"
$de.psbase.Invoke("Add",([ADSI]"WinNT://$domain/$user").path)
} catch {
write-host "User not added, already exists or not running as Administrator" -ForegroundColor Red
}
}
function Get-GroupBySid () {
param(
[parameter(Mandatory=$true,ValueFromPipeline=$true,ValueFromPipelineByPropertyName=$true)]
[Alias("Name")]
[string]$ComputerName,
[string]$GroupNameSid = "S-1-5-32-544"
)
$objSID = New-Object System.Security.Principal.SecurityIdentifier($GroupNameSid)
$objgroup = $objSID.Translate( [System.Security.Principal.NTAccount])
$objgroupname = ($objgroup.Value).Split("\")[1]
return ,$objgroupname
}
DoWork $gComputerName $gLookForBySid $gDomain $gUser
Successful script output
Checking group SID S-1-5-32-569 Adding User Evotec\user1 to group Cryptographic Operators Quitting. My job is done.
Something went wrong script output
Checking group SID S-1-5-32-569 Adding User Evotec\user1 to group Cryptographic Operators User not added, already exists or not running as Administrator Quitting. My job is done.
📖 Well-known SIDs
A security identifier (SID) is a unique value of variable length that is used to identify a security principal or security group in Windows operating systems. Well-known SIDs are a group of SIDs that identify generic users or generic groups. Their values remain constant across all operating systems.
This information is useful for troubleshooting issues that involve security. It is also useful for potential display problems that may be seen in the ACL editor. An SID may be displayed in the ACL editor instead of in the user or group name.
Well-known SIDs
- SID: S-1-0
Name: Null Authority
Description: An identifier authority. - SID: S-1-0-0
Name: Nobody
Description: No security principal. - SID: S-1-1
Name: World Authority
Description: An identifier authority. - SID: S-1-1-0
Name: Everyone
Description: A group that includes all users, even anonymous users and guests. Membership is controlled by the operating system.
Note By default, the Everyone group no longer includes anonymous users on a computer that is running Windows XP Service Pack 2 (SP2).
- SID: S-1-2
Name: Local Authority
Description: An identifier authority. - SID: S-1-2-0
Name: Local
Description: A group that includes all users who have logged on locally. - SID: S-1-2-1
Name: Console Logon
Description: A group that includes users who are logged on to the physical console.
Note Added in Windows 7 and Windows Server 2008 R2
- SID: S-1-3
Name: Creator Authority
Description: An identifier authority. - SID: S-1-3-0
Name: Creator Owner
Description: A placeholder in an inheritable access control entry (ACE). When the ACE is inherited, the system replaces this SID with the SID for the object's creator. - SID: S-1-3-1
Name: Creator Group
Description: A placeholder in an inheritable ACE. When the ACE is inherited, the system replaces this SID with the SID for the primary group of the object's creator. The primary group is used only by the POSIX subsystem. - SID: S-1-3-2
Name: Creator Owner Server
Description: This SID is not used in Windows 2000. - SID: S-1-3-3
Name: Creator Group Server
Description: This SID is not used in Windows 2000. - SID: S-1-3-4 Name: Owner Rights
Description: A group that represents the current owner of the object. When an ACE that carries this SID is applied to an object, the system ignores the implicit READ_CONTROL and WRITE_DAC permissions for the object owner. - SID: S-1-5-80-0
Name: All Services
Description: A group that includes all service processes configured on the system. Membership is controlled by the operating system.
Note Added in Windows Vista and Windows Server 2008
- SID: S-1-4
Name: Non-unique Authority
Description: An identifier authority. - SID: S-1-5
Name: NT Authority
Description: An identifier authority. - SID: S-1-5-1
Name: Dialup
Description: A group that includes all users who have logged on through a dial-up connection. Membership is controlled by the operating system. - SID: S-1-5-2
Name: Network
Description: A group that includes all users that have logged on through a network connection. Membership is controlled by the operating system. - SID: S-1-5-3
Name: Batch
Description: A group that includes all users that have logged on through a batch queue facility. Membership is controlled by the operating system. - SID: S-1-5-4
Name: Interactive
Description: A group that includes all users that have logged on interactively. Membership is controlled by the operating system. - SID: S-1-5-5-X-Y
Name: Logon Session
Description: A logon session. The X and Y values for these SIDs are different for each session. - SID: S-1-5-6
Name: Service
Description: A group that includes all security principals that have logged on as a service. Membership is controlled by the operating system. - SID: S-1-5-7
Name: Anonymous
Description: A group that includes all users that have logged on anonymously. Membership is controlled by the operating system. - SID: S-1-5-8
Name: Proxy
Description: This SID is not used in Windows 2000. - SID: S-1-5-9
Name: Enterprise Domain Controllers
Description: A group that includes all domain controllers in a forest that uses an Active Directory directory service. Membership is controlled by the operating system. - SID: S-1-5-10
Name: Principal Self
Description: A placeholder in an inheritable ACE on an account object or group object in Active Directory. When the ACE is inherited, the system replaces this SID with the SID for the security principal who holds the account. - SID: S-1-5-11
Name: Authenticated Users
Description: A group that includes all users whose identities were authenticated when they logged on. Membership is controlled by the operating system. - SID: S-1-5-12
Name: Restricted Code
Description: This SID is reserved for future use. - SID: S-1-5-13
Name: Terminal Server Users
Description: A group that includes all users that have logged on to a Terminal Services server. Membership is controlled by the operating system. - SID: S-1-5-14
Name: Remote Interactive Logon
Description: A group that includes all users who have logged on through a terminal services logon. - SID: S-1-5-15
Name: This Organization
Description: A group that includes all users from the same organization. Only included with AD accounts and only added by a Windows Server 2003 or later domain controller. - SID: S-1-5-17
Name: This Organization
Description: An account that is used by the default Internet Information Services (IIS) user. - SID: S-1-5-18
Name: Local System
Description: A service account that is used by the operating system. - SID: S-1-5-19
Name: NT Authority
Description: Local Service - SID: S-1-5-20
Name: NT Authority
Description: Network Service - SID: S-1-5-21domain-500
Name: Administrator
Description: A user account for the system administrator. By default, it is the only user account that is given full control over the system. - SID: S-1-5-21domain-501
Name: Guest
Description: A user account for people who do not have individual accounts. This user account does not require a password. By default, the Guest account is disabled. - SID: S-1-5-21domain-502
Name: KRBTGT
Description: A service account that is used by the Key Distribution Center (KDC) service. - SID: S-1-5-21domain-512
Name: Domain Admins
Description: A global group whose members are authorized to administer the domain. By default, the Domain Admins group is a member of the Administrators group on all computers that have joined a domain, including the domain controllers. Domain Admins is the default owner of any object that is created by any member of the group. - SID: S-1-5-21domain-513
Name: Domain Users
Description: A global group that, by default, includes all user accounts in a domain. When you create a user account in a domain, it is added to this group by default. - SID: S-1-5-21domain-514
Name: Domain Guests
Description: A global group that, by default, has only one member, the domain's built-in Guest account. - SID: S-1-5-21domain-515
Name: Domain Computers
Description: A global group that includes all clients and servers that have joined the domain. - SID: S-1-5-21domain-516
Name: Domain Controllers
Description: A global group that includes all domain controllers in the domain. New domain controllers are added to this group by default. - SID: S-1-5-21domain-517
Name: Cert Publishers
Description: A global group that includes all computers that are running an enterprise certification authority. Cert Publishers are authorized to publish certificates for User objects in Active Directory. - SID: S-1-5-21root domain-518
Name: Schema Admins
Description: A universal group in a native-mode domain; a global group in a mixed-mode domain. The group is authorized to make schema changes in Active Directory. By default, the only member of the group is the Administrator account for the forest root domain. - SID: S-1-5-21root domain-519
Name: Enterprise Admins
Description: A universal group in a native-mode domain; a global group in a mixed-mode domain. The group is authorized to make forest-wide changes in Active Directory, such as adding child domains. By default, the only member of the group is the Administrator account for the forest root domain. - SID: S-1-5-21domain-520
Name: Group Policy Creator Owners
Description: A global group that is authorized to create new Group Policy objects in Active Directory. By default, the only member of the group is Administrator. - SID: S-1-5-21domain-553
Name: RAS and IAS Servers
Description: A domain local group. By default, this group has no members. Servers in this group have Read Account Restrictions and Read Logon Information access to User objects in the Active Directory domain local group. - SID: S-1-5-32-544
Name: Administrators
Description: A built-in group. After the initial installation of the operating system, the only member of the group is the Administrator account. When a computer joins a domain, the Domain Admins group is added to the Administrators group. When a server becomes a domain controller, the Enterprise Admins group also is added to the Administrators group. - SID: S-1-5-32-545
Name: Users
Description: A built-in group. After the initial installation of the operating system, the only member is the Authenticated Users group. When a computer joins a domain, the Domain Users group is added to the Users group on the computer. - SID: S-1-5-32-546
Name: Guests
Description: A built-in group. By default, the only member is the Guest account. The Guests group allows occasional or one-time users to log on with limited privileges to a computer's built-in Guest account. - SID: S-1-5-32-547
Name: Power Users
Description: A built-in group. By default, the group has no members. Power users can create local users and groups; modify and delete accounts that they have created; and remove users from the Power Users, Users, and Guests groups. Power users also can install programs; create, manage, and delete local printers; and create and delete file shares. - SID: S-1-5-32-548
Name: Account Operators
Description: A built-in group that exists only on domain controllers. By default, the group has no members. By default, Account Operators have permission to create, modify, and delete accounts for users, groups, and computers in all containers and organizational units of Active Directory except the Builtin container and the Domain Controllers OU. Account Operators do not have permission to modify the Administrators and Domain Admins groups, nor do they have permission to modify the accounts for members of those groups. - SID: S-1-5-32-549
Name: Server Operators
Description: A built-in group that exists only on domain controllers. By default, the group has no members. Server Operators can log on to a server interactively; create and delete network shares; start and stop services; back up and restore files; format the hard disk of the computer; and shut down the computer. - SID: S-1-5-32-550
Name: Print Operators
Description: A built-in group that exists only on domain controllers. By default, the only member is the Domain Users group. Print Operators can manage printers and document queues. - SID: S-1-5-32-551
Name: Backup Operators
Description: A built-in group. By default, the group has no members. Backup Operators can back up and restore all files on a computer, regardless of the permissions that protect those files. Backup Operators also can log on to the computer and shut it down. - SID: S-1-5-32-552
Name: Replicators
Description: A built-in group that is used by the File Replication service on domain controllers. By default, the group has no members. Do not add users to this group. - SID: S-1-5-64-10
Name: NTLM Authentication
Description: A SID that is used when the NTLM authentication package authenticated the client - SID: S-1-5-64-14
Name: SChannel Authentication
Description: A SID that is used when the SChannel authentication package authenticated the client. - SID: S-1-5-64-21
Name: Digest Authentication
Description: A SID that is used when the Digest authentication package authenticated the client. - SID: S-1-5-80
Name: NT Service
Description: An NT Service account prefix - SID: S-1-5-80-0
SID S-1-5-80-0 = NT SERVICES\ALL SERVICES
Name: All Services
Description: A group that includes all service processes that are configured on the system. Membership is controlled by the operating system.
Note Added in Windows Server 2008 R2
- SID: S-1-5-83-0
Name: NT VIRTUAL MACHINE\Virtual Machines
Description: A built-in group. The group is created when the Hyper-V role is installed. Membership in the group is maintained by the Hyper-V Management Service (VMMS). This group requires the “Create Symbolic Links” right (SeCreateSymbolicLinkPrivilege), and also the “Log on as a Service” right (SeServiceLogonRight).
Note Added in Windows 8 and Windows Server 2012
- SID: S-1-16-0
Name: Untrusted Mandatory Level
Description: An untrusted integrity level. Note Added in Windows Vista and Windows Server 2008
Note Added in Windows Vista and Windows Server 2008
- SID: S-1-16-4096
Name: Low Mandatory Level
Description: A low integrity level.
Note Added in Windows Vista and Windows Server 2008
- SID: S-1-16-8192
Name: Medium Mandatory Level
Description: A medium integrity level.
Note Added in Windows Vista and Windows Server 2008
- SID: S-1-16-8448
Name: Medium Plus Mandatory Level
Description: A medium plus integrity level.
Note Added in Windows Vista and Windows Server 2008
- SID: S-1-16-12288
Name: High Mandatory Level
Description: A high integrity level.
Note Added in Windows Vista and Windows Server 2008
- SID: S-1-16-16384
Name: System Mandatory Level
Description: A system integrity level.
Note Added in Windows Vista and Windows Server 2008
- SID: S-1-16-20480
Name: Protected Process Mandatory Level
Description: A protected-process integrity level.
Note Added in Windows Vista and Windows Server 2008
- SID: S-1-16-28672
Name: Secure Process Mandatory Level
Description: A secure process integrity level.
Note Added in Windows Vista and Windows Server 2008
Well-known SIDs Windows 2003 Domain Controller
The following groups appear as SIDs until a Windows Server 2003 domain controller is made the primary domain controller (PDC) operations master role holder. The “operations master” is also known as flexible single master operations (FSMO). The following additional built-in groups are created when a Windows Server 2003 domain controller is added to the domain:
- SID: S-1-5-32-554
Name: BUILTIN\Pre-Windows 2000 Compatible Access
Description: An alias added by Windows 2000. A backward compatibility group which allows read access on all users and groups in the domain. - SID: S-1-5-32-555
Name: BUILTIN\Remote Desktop Users
Description: An alias. Members in this group are granted the right to logon remotely. - SID: S-1-5-32-556
Name: BUILTIN\Network Configuration Operators
Description: An alias. Members in this group can have some administrative privileges to manage configuration of networking features. - SID: S-1-5-32-557
Name: BUILTIN\Incoming Forest Trust Builders
Description: An alias. Members of this group can create incoming, one-way trusts to this forest. - SID: S-1-5-32-558
Name: BUILTIN\Performance Monitor Users
Description: An alias. Members of this group have remote access to monitor this computer. - SID: S-1-5-32-559
Name: BUILTIN\Performance Log Users
Description: An alias. Members of this group have remote access to schedule logging of performance counters on this computer. - SID: S-1-5-32-560
Name: BUILTIN\Windows Authorization Access Group
Description: An alias. Members of this group have access to the computed tokenGroupsGlobalAndUniversal attribute on User objects. - SID: S-1-5-32-561
Name: BUILTIN\Terminal Server License Servers
Description: An alias. A group for Terminal Server License Servers. When Windows Server 2003 Service Pack 1 is installed, a new local group is created. - SID: S-1-5-32-562
Name: BUILTIN\Distributed COM Users
Description: An alias. A group for COM to provide computerwide access controls that govern access to all call, activation, or launch requests on the computer.
Well-known SIDs Windows 2008 Domain Controller
The following groups appear as SIDs until a Windows Server 2008 or Windows Server 2008 R2 domain controller is made the primary domain controller (PDC) operations master role holder. The “operations master” is also known as flexible single master operations (FSMO). The following additional built-in groups are created when a Windows Server 2008 or Windows Server 2008 R2 domain controller is added to the domain:
- SID: S-1-5- 21domain -498
Name: Enterprise Read-only Domain Controllers
Description: A Universal group. Members of this group are Read-Only Domain Controllers in the enterprise - SID: S-1-5- 21domain -521
Name: Read-only Domain Controllers
Description: A Global group. Members of this group are Read-Only Domain Controllers in the domain - SID: S-1-5-32-569
Name: BUILTIN\Cryptographic Operators
Description: A Builtin Local group. Members are authorized to perform cryptographic operations. - SID: S-1-5-21 domain -571
Name: Allowed RODC Password Replication Group
Description: A Domain Local group. Members in this group can have their passwords replicated to all read-only domain controllers in the domain. - SID: S-1-5- 21 domain -572
Name: Denied RODC Password Replication Group
Description: A Domain Local group. Members in this group cannot have their passwords replicated to any read-only domain controllers in the domain - SID: S-1-5-32-573
Name: BUILTIN\Event Log Readers
Description: A Builtin Local group. Members of this group can read event logs from local machine. - SID: S-1-5-32-574
Name: BUILTIN\Certificate Service DCOM Access
Description: A Builtin Local group. Members of this group are allowed to connect to Certification Authorities in the enterprise.
Well-known SIDs Windows 2012 Domain Controller
The following groups appear as SIDs until a Windows Server 2012 domain controller is made the primary domain controller (PDC) operations master role holder. The “operations master” is also known as flexible single master operations (FSMO). The following additional built-in groups are created when a Windows Server 2012 domain controller is added to the domain:
- SID: S-1-5-21-domain-522
Name: Cloneable Domain Controllers
Description: A Global group. Members of this group that are domain controllers may be cloned. - SID: S-1-5-32-575
Name: BUILTIN\RDS Remote Access Servers
Description: A Builtin Local group. Servers in this group enable users of RemoteApp programs and personal virtual desktops access to these resources. In Internet-facing deployments, these servers are typically deployed in an edge network. This group needs to be populated on servers running RD Connection Broker. RD Gateway servers and RD Web Access servers used in the deployment need to be in this group. - SID: S-1-5-32-576
Name: BUILTIN\RDS Endpoint Servers
Description: A Builtin Local group. Servers in this group run virtual machines and host sessions where users RemoteApp programs and personal virtual desktops run. This group needs to be populated on servers running RD Connection Broker. RD Session Host servers and RD Virtualization Host servers used in the deployment need to be in this group. - SID: S-1-5-32-577
Name: BUILTIN\RDS Management Servers
Description: A Builtin Local group. Servers in this group can perform routine administrative actions on servers running Remote Desktop Services. This group needs to be populated on all servers in a Remote Desktop Services deployment. The servers running the RDS Central Management service must be included in this group. - SID: S-1-5-32-578
Name: BUILTIN\Hyper-V Administrators
Description: A Builtin Local group. Members of this group have complete and unrestricted access to all features of Hyper-V. - SID: S-1-5-32-579
Name: BUILTIN\Access Control Assistance Operators
Description: A Builtin Local group. Members of this group can remotely query authorization attributes and permissions for resources on this computer. - SID: S-1-5-32-580
Name: BUILTIN\Remote Management Users
Description: A Builtin Local group. Members of this group can access WMI resources over management protocols (such as WS-Management via the Windows Remote Management service). This applies only to WMI namespaces that grant access to the user.